US Weapon Systems: Vulnerabilities Exposed
The United States boasts one of the most advanced and diverse arrays…
Uncovering Military Cyber Security Failures
Military cyber security has emerged as a critical component of national defense…
Optimizing Patch Cadence for Contractor Efficiency
Patch cadence refers to the frequency and regularity with which software updates,…
Implementing Zero Trust in Military Operations
In the realm of military operations, the concept of Zero Trust has…
Revolutionizing F-35 Logistics: ALIS ODIN System
The F-35 Lightning II, a fifth-generation multirole stealth fighter, represents a significant…
The F-35 Grounded: Technical Issues and Safety Concerns
The F-35 Lightning II, a fifth-generation multirole stealth fighter, has been at…
Securing the Abrams Tank: Diagnostic Password Protection
In the realm of military technology, the Abrams Tank stands as a…
Enhancing Naval Capabilities with Littoral Combat Ship Mission Modules
The Littoral Combat Ship (LCS) represents a significant evolution in naval warfare,…
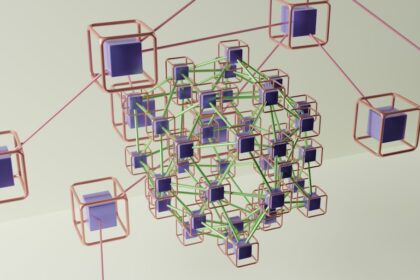
JADC2 Network Vulnerability: A Critical Security Threat
Joint All-Domain Command and Control (JADC2) represents a transformative approach to military…
Contractors’ Dominance at the Pentagon
In recent decades, the presence of private contractors within the Pentagon has…