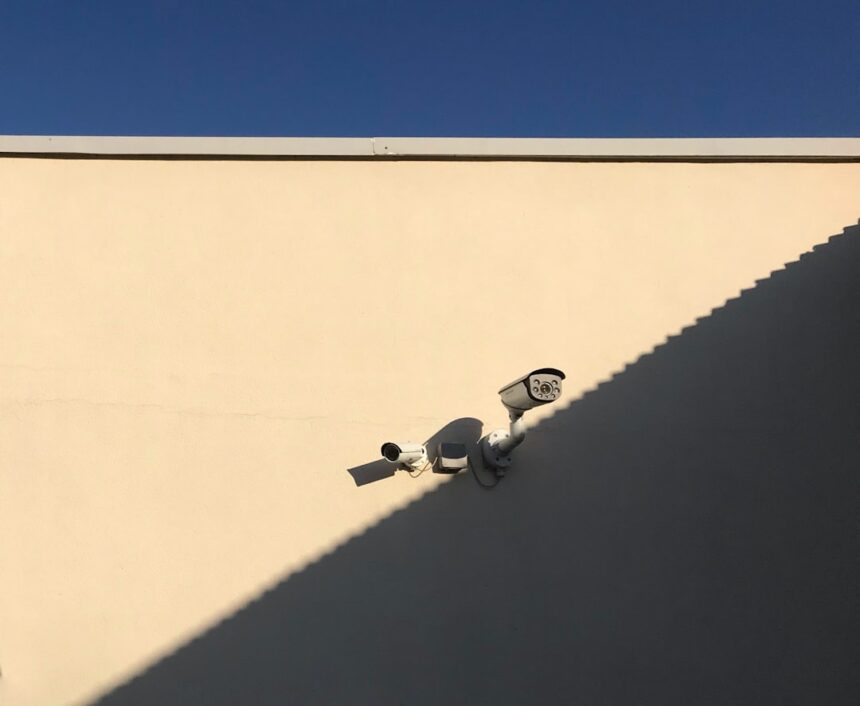
The increasing prominence of “shadow intelligence units” within the United States government is a complex development, driven by evolving threats, technological advancements, and shifts in strategic priorities. These units, often operating with less public visibility and sometimes outside traditional bureaucratic structures, are designed to address specific, often sensitive, national security challenges. Their rise is not a monolithic phenomenon but rather a web of interconnected initiatives, each with its own rationale, operational methods, and implications for oversight and accountability.
The nature of threats facing the United States has become increasingly multifaceted and dynamic in the post-Cold War era. The decline of large-scale conventional military confrontation has paradoxically led to a proliferation of unconventional, asymmetric, and often diffuse challenges. This necessitates a more agile and specialized approach to intelligence gathering and analysis.
Asymmetric Warfare and Non-State Actors
The rise of terrorist organizations, transnational criminal syndicates, and other non-state actors equipped with advanced technologies and operating across borders has fundamentally altered the intelligence calculus. These groups often evade traditional state-centric surveillance methods, requiring highly adapted and discreet intelligence operations.
The Need for Specialized Tactical Intelligence
Traditional intelligence agencies, while robust in their strategic analysis, can sometimes be less adept at providing immediate, on-the-ground tactical intelligence required for counter-terrorism operations or the disruption of illicit networks. Shadow units are often formed to fill this gap, focusing on the granular details of enemy movements, capabilities, and intentions.
Cyber and Information Warfare
The digital domain has emerged as a primary battlefield. State and non-state actors alike engage in sophisticated cyberattacks, disinformation campaigns, and the manipulation of information to achieve political and strategic objectives. This has spurred the creation of intelligence capabilities specifically designed to operate within and defend against these digital threats.
Deep Dive into the Digital Shadow
Understanding the motivations and capabilities of actors operating in cyberspace requires specialized technical expertise and methodologies. Shadow intelligence units often house these highly trained individuals, capable of penetrating secure networks, analyzing vast data streams, and identifying nascent cyber threats before they materialize into significant disruptions.
Hybrid Warfare and Gray Zone Conflicts
The concept of “hybrid warfare” encompasses a spectrum of conflict that blurs the lines between peace and war, utilizing a combination of conventional and unconventional tactics. This includes economic coercion, political subversion, disinformation, and proxy warfare. Addressing these challenges requires intelligence operations that can operate below the threshold of overt conflict.
Operating in Ambiguous Environments
Shadow units are often tasked with gathering intelligence in what are sometimes referred to as “gray zones” – environments where attribution is difficult and direct confrontation is undesirable. This requires a delicate balance of deniability, precision, and strategic patience.
Shadow intelligence units within the U.S. government have garnered significant attention due to their clandestine operations and the implications they have for national security and civil liberties. For a deeper understanding of these units and their impact on intelligence practices, you can read the article available at this link. The article explores the complexities surrounding these secretive organizations and their role in contemporary intelligence gathering.
The Genesis and Categorization of Shadow Units
The term “shadow intelligence units” is not officially recognized by the US government and is largely a descriptive term used in public discourse and analysis. These entities can emerge from various parts of the national security apparatus, each with its own distinct origin and mandate.
Offshoots of Traditional Agencies
Many shadow units are, in fact, highly specialized sub-components of larger, established intelligence agencies like the Central Intelligence Agency (CIA), the National Security Agency (NSA), or the Defense Intelligence Agency (DIA). These units are often created to focus on a particular mission or technology.
Elite Task Forces and Special Operations Components
Within these agencies, specific task forces or specialized groups may be established to tackle high-priority missions that require a level of focus and discretion beyond the scope of their parent organization. These might involve covert action, specialized technical operations, or the analysis of highly sensitive data.
Independent or Semi-Autonomous Organizations
In some instances, shadow units may be established with a degree of semi-autonomy, reporting directly to a high-level official or a specific policy-making body rather than being fully integrated into the operational hierarchy of a traditional intelligence agency.
Innovation Hubs and Rapid Response Teams
These more independent entities might be conceived as innovation hubs, designed to test new methodologies or technologies outside the established bureaucratic constraints. They can also function as rapid response teams to emergent crises, bypassing formal approval processes for quicker deployment of intelligence assets.
Interagency and Joint Ventures
The complexities of modern threats often necessitate collaboration between different branches of government. Shadow units can take the form of interagency or joint ventures, pooling resources and expertise from multiple departments or agencies to address a common challenge.
Cross-Functional Coalitions for Specific Threats
These ventures might involve personnel from intelligence agencies, law enforcement, the military, and even civilian departments, working together under a unified command or coordinating structure for a specific long-term intelligence objective or a transient threat.
Operational Modalities and Methodologies
The operational methods of shadow intelligence units are as diverse as their origins, reflecting the unique challenges they are designed to address. Secrecy, adaptability, and technical proficiency are common threads.
Covert Action and Paramilitary Operations
A significant portion of shadow intelligence activity involves covert action, which can range from propaganda and political influence operations to more direct, paramilitary interventions. These operations are typically authorized at the highest levels of government.
Deniable Operations and Strategic Ambiguity
The hallmark of such operations is often deniability, allowing the US government to distance itself from any direct connection if the operation is compromised. This requires meticulous planning and execution, often involving third-party contractors or proxies.
Advanced Technical Espionage
The technological sophistication of adversaries and the increasing reliance on digital infrastructure have led to the rise of units focused on advanced technical espionage. This includes cyber penetration, signals intelligence, and the exploitation of vulnerabilities in critical systems.
Exploiting the Digital Frontier
These units employ highly skilled technicians and analysts who can develop novel methods for collecting intelligence in cyberspace, often in real-time, and analyze vast quantities of raw data for actionable insights.
Human Intelligence and Deep Cover Operations
Despite the technological advancements, human intelligence (HUMINT) remains crucial, particularly for understanding the intent and motivations of adversaries. Shadow units may engage in deep cover operations to cultivate sources and gather information in sensitive environments.
Cultivating Sources in Hostile Territories
This involves long-term agent recruitment, tradecraft development, and the establishment of complex networks in countries or organizations where direct access is impossible for overt intelligence gathering.
Open-Source Intelligence (OSINT) and Advanced Analysis
While “open-source” may sound non-covert, the sophisticated aggregation, analysis, and weaponization of publicly available information has become a critical component of modern intelligence. Shadow units may specialize in leveraging OSINT in novel ways.
Synthesizing Disparate Data Streams
These units excel at synthesizing information from a vast array of sources – social media, news reports, academic publications, satellite imagery – to identify patterns, predict trends, and understand the public sentiment or enemy plans.
Implications for Oversight and Accountability

The rise of shadow intelligence units presents significant challenges to traditional oversight and accountability mechanisms within the US government. The inherent secrecy, limited public visibility, and sometimes novel operational methodologies can create a disconnect between operational action and democratic scrutiny.
The Challenge of Congressional Oversight
Congressional committees responsible for intelligence oversight, such as the House and Senate Intelligence Committees, face a constant struggle to maintain adequate visibility into the activities of these often-discreet units.
Balancing Secrecy and Transparency
The need to protect sources and methods while still providing meaningful oversight is a delicate balancing act. Classified briefings and limited access to information can sometimes hinder the committees’ ability to fully understand the scope and impact of shadow operations.
Internal Agency Controls and Whistleblower Protections
Within the intelligence agencies themselves, internal controls and ethical guidelines are crucial for governing the activities of shadow units. The protection of whistleblowers who may uncover wrongdoing is also a critical element of maintaining accountability.
The Role of Inspectors General
Inspectors General within intelligence agencies are tasked with independent oversight of agency activities. Their role in investigating allegations of abuse or mismanagement within shadow units is vital, though their effectiveness can be hampered by secrecy.
The Public’s Right to Know vs. National Security Imperatives
The existence of these units, their missions, and their activities often operate outside the purview of public knowledge. This raises fundamental questions about the balance between the public’s right to know and the government’s imperative to protect national security.
Navigating the Information Asymmetry
The significant information asymmetry between the government and the public regarding these units poses a challenge for informed democratic discourse and debate about national security policy.
Shadow intelligence units within the US government have garnered significant attention for their covert operations and the implications they hold for national security. For a deeper understanding of the complexities surrounding these units, you can explore a related article that delves into their roles and the controversies they spark. The insights provided in this piece can help illuminate the often opaque nature of intelligence work. To read more about this topic, visit this article for an in-depth analysis.
The Future Trajectory of Shadow Intelligence
| Agency | Number of Units | Mission |
|---|---|---|
| CIA | Unknown | Covert intelligence gathering and analysis |
| NSA | Unknown | Signals intelligence and cybersecurity |
| Defense Intelligence Agency (DIA) | Unknown | Military intelligence and counterintelligence |
| FBI Special Surveillance Group (SSG) | Unknown | Covert surveillance and intelligence operations |
The continued evolution of global threats and technological advancements suggests that the rise of shadow intelligence units is likely to persist, if not accelerate. The US government will continue to adapt its intelligence capabilities to meet these evolving challenges.
Technological Determinism and Intelligence Evolution
The relentless march of technology – artificial intelligence, quantum computing, advanced data analytics, and biotechnology – will undoubtedly shape the future of intelligence gathering and analysis, necessitating the creation of new specialized units.
The Algorithmic Intelligence Frontier
The increasing reliance on algorithms for data analysis, prediction, and even operation automation will likely lead to the formation of units dedicated to the development and deployment of such technologies for intelligence purposes.
The Geopolitical Landscape and Strategic Adaptation
Shifts in the global geopolitical landscape, including the rise of new powers, renewed great power competition, and ongoing regional conflicts, will continue to drive the demand for specialized and adaptable intelligence capabilities.
Proactive Intelligence for Predatory Regimes
The intelligence community will likely need to develop units specifically tasked with understanding and countering the increasingly sophisticated intelligence operations of adversarial states, often employing hybrid and asymmetric tactics.
The Ethical and Legal Quagmire
As shadow intelligence units become more integral to national security, the ethical and legal questions surrounding their operation will only become more pronounced. Defining the boundaries of acceptable covert action, ensuring robust oversight, and grappling with the implications of advanced surveillance technologies will be ongoing challenges.
The Unseen Hand of Statecraft
These units, by their very nature, operate in the unseen spaces of statecraft. Their continued development will demand careful consideration of their role in a democratic society, ensuring that their pursuit of national security does not undermine the very principles they are meant to protect. The rise of shadow intelligence units is not a signal of an anomaly, but rather an indicator of the ongoing, often complex, transformation of national security in the 21st century.
FAQs
What are shadow intelligence units in the US government?
Shadow intelligence units in the US government are covert or clandestine groups within intelligence agencies that operate outside of the public eye and often carry out sensitive or classified operations.
How are shadow intelligence units different from regular intelligence units?
Shadow intelligence units differ from regular intelligence units in that they often operate with a higher level of secrecy and are tasked with carrying out more covert or sensitive operations. They may also have less oversight and accountability compared to regular intelligence units.
Which US government agencies have shadow intelligence units?
It is widely believed that various US government agencies, including the CIA, NSA, and DIA, have shadow intelligence units. However, due to the secretive nature of these units, specific details about their existence and operations are often classified.
What types of operations do shadow intelligence units typically carry out?
Shadow intelligence units may be involved in a wide range of operations, including espionage, sabotage, covert action, and intelligence gathering. These units may also be involved in cyber operations and other forms of clandestine activities.
What are the implications of shadow intelligence units for US national security?
The existence of shadow intelligence units raises concerns about accountability, oversight, and the potential for abuse of power. While these units may be necessary for certain sensitive operations, there is also a risk that their activities could undermine democratic principles and the rule of law.