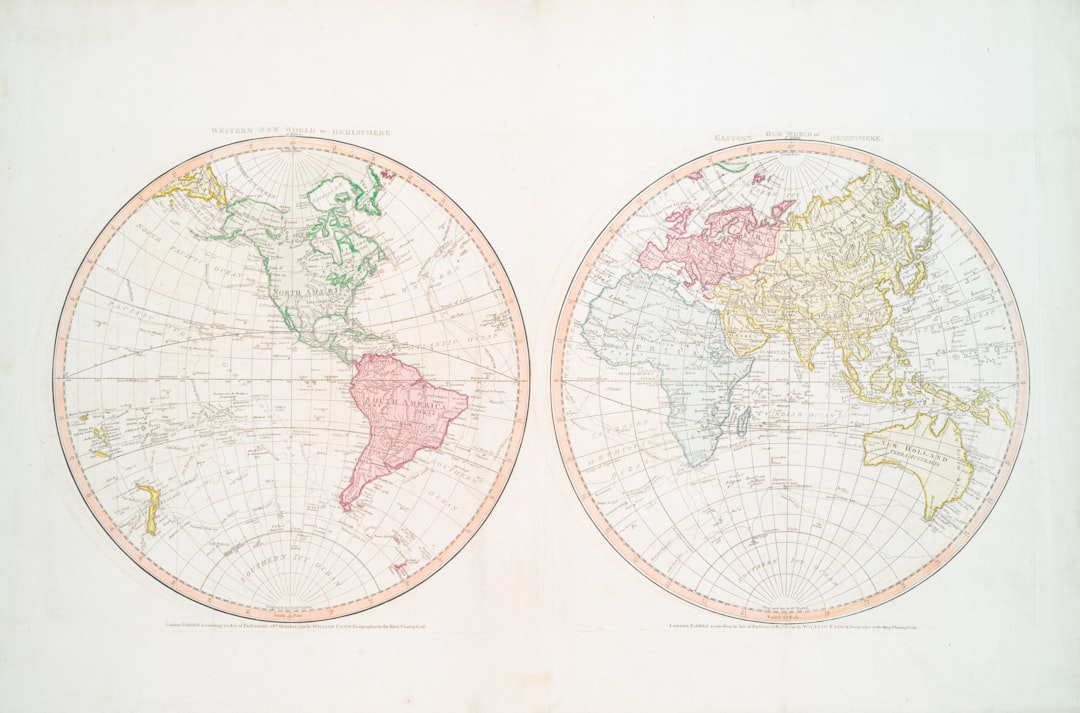
The Cold War, a geopolitical struggle spanning from the mid-20th century, was characterized not by direct military confrontation between the United States and the Soviet Union, but by an intricate dance of proxies, ideology, and, significantly, technological one-upmanship. Beneath the surface of political posturing and nuclear brinkmanship lay a battle fought in laboratories, design bureaus, and, more clandestinely, through espionage. This article explores the phenomenon of technological theft during the Cold War, a period where the acquisition of an adversary’s innovations could significantly shift the balance of power.
The close of World War II left the victorious powers with a stark realization: the nation with superior technology held an undeniable advantage. The V-2 rocket program of Nazi Germany, for instance, offered a terrifying glimpse into the future of warfare, prompting both the Soviets and the Americans to scramble for German scientists and their research. This initial race set a precedent for the decades to come. Each side viewed the other’s technological progress with a mixture of suspicion and desire, leading to the institutionalization of intelligence gathering focused explicitly on scientific and engineering advancements.
Operation Paperclip and its Soviet Counterpart
Operation Paperclip, the secret post-WWII program by the United States to recruit German scientists, engineers, and technicians, particularly those involved in rocketry, aircraft design, and ballistics, is a well-documented example of this foundational scramble. Wernher von Braun, a central figure in the Nazi rocket program, became instrumental in the American space effort, directly contributing to the Mercury, Gemini, and Apollo programs.
Conversely, the Soviet Union conducted its own similar clandestine operations, often referred to as “trophy brigades.” These brigades systematically plundered German factories, research facilities, and intellectual property, relocating them to the Soviet Union. Entire factories were dismantled and reassembled, and thousands of German scientists and engineers were forcibly or willingly relocated to Soviet territories to contribute to their burgeoning military and industrial complex. This direct appropriation of German expertise laid the groundwork for the Soviet Union’s rapid development in areas like jet propulsion and rocketry.
The Cold War era was marked by intense espionage and technological competition, leading to numerous secret operations aimed at acquiring advanced technologies. A fascinating article that delves into one such operation is available at In the War Room, where it explores the intricacies of a high-stakes heist involving cutting-edge military technology. This piece provides insight into the motivations behind these covert actions and the lengths to which nations would go to secure an advantage during this tumultuous period in history.
The Atomic Gambit: A Race Against Time
Perhaps the most pivotal technological secret of the early Cold War was the atomic bomb. The United States’ successful detonation and subsequent use of atomic weapons in 1945 sent shockwaves across the globe, fundamentally altering the strategic landscape. The Soviets understood that possessing their own atomic arsenal was paramount to achieving parity and deterring a potential American first strike. This understanding fueled an intense and ruthlessly efficient espionage effort.
The Rosenberg Network and Klaus Fuchs
The Soviet intelligence apparatus, already adept at clandestine operations, intensified its efforts to penetrate the Manhattan Project, the top-secret American program to develop atomic weapons. Key figures emerged from the shadows to provide crucial blueprints and scientific data. Julius and Ethel Rosenberg, American citizens convicted and executed for espionage, were alleged to have played a role in transmitting atomic secrets.
More significantly, however, was the contribution of Klaus Fuchs, a German-born theoretical physicist and Soviet spy who worked on the Manhattan Project. Fuchs provided the Soviet Union with highly detailed information about the design of the atomic bomb, including crucial calculations and details about the implosion device used in the Trinity test. His betrayal is often credited with significantly accelerating the Soviet atomic bomb program, potentially shortening its development by several years. This act of espionage was a direct heist of intellectual property, a transfer of knowledge that had immense geopolitical consequences. The Soviet Union’s first atomic bomb test in 1949, far sooner than many in the West expected, was a testament to the effectiveness of their espionage efforts.
The Aerospace Arena: Wings of Deception
With the advent of the nuclear age, the delivery systems for these devastating weapons became a primary focus. Long-range bombers and, later, intercontinental ballistic missiles (ICBMs) represented the cutting edge of military technology. The aerospace industry became a new battleground for technological theft, with each side desperately seeking to replicate or counter the other’s advancements.
Reverse Engineering and the MIGs
The Soviet Union, initially lagging behind in certain aspects of jet aircraft technology, placed a high priority on acquiring Western designs. When a British Rolls-Royce Nene jet engine, initially sold to the Soviets for civilian aircraft, was reverse-engineered and subsequently powered the formidable MiG-15 fighter jet during the Korean War, it provided a stark illustration of these practices. This was not a direct heist in the traditional sense, but a strategic acquisition followed by meticulous deconstruction and replication, a form of industrial espionage on a grand scale.
Similarly, the United States was keen to get its hands on Soviet aerospace technology. The capture of functional Soviet aircraft, especially during conflicts like the Korean and Vietnam Wars, was a high priority. When a North Korean defector flew a MiG-15 to an American airbase in 1953 (Operation Moolah), it provided invaluable intelligence. American engineers and test pilots meticulously examined the aircraft, studying its strengths and weaknesses, which directly informed the design of future American fighter jets. This was a technological windfall, allowing the U.S. to “look under the hood” of their adversary’s cutting-edge machinery.
The Electronic Frontier: Whispers in the Wires
As the Cold War progressed, the focus of technological competition expanded beyond physical weapons to encompass the burgeoning fields of electronics, computing, and communications. Surveillance technology, encryption devices, and guidance systems became crucial components of national security. The abstraction of information made these areas particularly susceptible to espionage, often requiring less physical theft and more intellectual penetration.
The F-117 Nighthawk and “Black Projects”
While not a direct instance of theft by the Soviets from the U.S., the extreme secrecy surrounding projects like the F-117 Nighthawk stealth fighter demonstrates the intensity of the desire to protect cutting-edge technology. The development of stealth technology was a closely guarded secret, a “black project” kept hidden from public view and, crucially, from Soviet intelligence. The unique faceted design and radar-absorbing materials of the F-117 represented a paradigm shift in aerial warfare. The Soviet Union, aware of such developments through various intelligence channels, invested heavily in developing counter-stealth technologies and their own stealth aircraft, highlighting the constant arms race fueled by both observation and suspicion. The very existence of such projects created an environment where the absence of knowledge became a driving force for espionage.
Conversely, the Soviet Union also pioneered advanced electronic warfare and radar systems. The U.S. invested significant resources in acquiring details of these systems, often through classified missions to recover downed Soviet aircraft or through human intelligence. Understanding the frequency ranges, signal patterns, and capabilities of Soviet radar systems was vital for developing effective countermeasures and ensuring the survivability of American aircraft. This was a constant battle of electronic wits, where a critical piece of information could render an entire system vulnerable.
The intrigue surrounding Cold War espionage often leads to discussions about the various secret technology heists that took place during that era. One fascinating case involves the theft of advanced military technology, which significantly impacted the balance of power between superpowers. For those interested in exploring this topic further, a related article can be found at this link, where you can delve deeper into the strategies and outcomes of these covert operations.
The Future of Warfare: From Satellites to Supercomputers
| Year | Operation Name | Country Involved | Technology Targeted | Outcome | Significance |
|---|---|---|---|---|---|
| 1945 | Operation Paperclip | USA | German Rocket Technology (V-2) | Successful | Accelerated US missile and space programs |
| 1946 | Operation Matchbox | USA | German Jet Engine Technology | Successful | Advanced US jet propulsion development |
| 1950 | Operation Gold | USA & UK | Soviet Communications Interception | Compromised (Soviet double agent) | Provided intelligence on Soviet communications |
| 1953 | Operation Mincemeat | UK | Deception Technology (Fake Documents) | Successful | Misled Soviet intelligence on Allied plans |
| 1960 | U-2 Spy Plane Incident | USA | High-altitude Reconnaissance Technology | Failed (Plane shot down) | Exposed US espionage efforts to Soviets |
| 1979 | Operation RYAN | USSR | US Nuclear Launch Protocols | Unsuccessful | Heightened Cold War tensions |
The latter stages of the Cold War saw an acceleration in the development of sophisticated technologies that would define future conflicts. Satellite reconnaissance, advanced computing, and precision-guided munitions became the new frontiers. The stakes remained incredibly high, as mastery in these areas promised unparalleled strategic advantages.
The A-12 Oxcart and Satellite Imagery
The development of the A-12 Oxcart and later the SR-71 Blackbird spy planes by the United States represented an astonishing leap in reconnaissance capabilities. These aircraft, capable of Mach 3+ speeds and flying at altitudes exceeding 80,000 feet, were designed to penetrate Soviet airspace and gather intelligence with unparalleled precision. The technology behind their engines, airframe materials, and camera systems was revolutionary, and consequently, a prime target for Soviet intelligence.
Simultaneously, the space race evolved into a battle for supremacy in satellite technology. The launch of Sputnik in 1957 shocked the West, demonstrating Soviet capabilities in rocketry and underscoring the potential for orbital surveillance. Both sides then embarked on ambitious programs to develop increasingly sophisticated reconnaissance satellites capable of providing high-resolution imagery and electronic intelligence. The designs of these satellites, their camera specifications, and their orbital mechanics became tightly held secrets, constantly threatened by espionage. The ability to peer into the adversary’s territory from space provided an unprecedented “over-the-shoulder” view, a constant low-level technological heist of information, without ever physically breaking into a lab. The development of a superior camera lens or a more resilient satellite body was thus as valuable as a nuclear warhead in the context of intelligence gathering.
Silicon and State Secrets
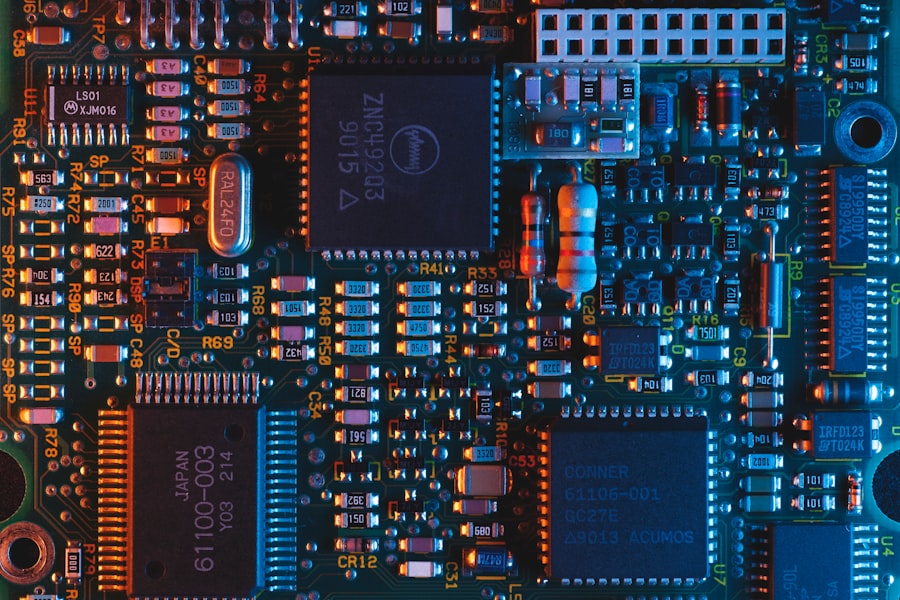
By the 1980s, the emergence of microelectronics and computing profoundly influenced military capabilities. Supercomputers, advanced integrated circuits, and software algorithms became critical for everything from ballistic missile guidance to cryptographic analysis. The theft of blueprints for advanced microprocessors or the source code for military software could have catastrophic consequences for national security.
The COCOM (Coordinating Committee for Multilateral Export Controls) restrictions implemented by Western nations aimed to prevent the transfer of militarily sensitive technologies to the Eastern Bloc. However, Soviet intelligence agencies like the KGB employed sophisticated networks to circumvent these controls, often acquiring Western computers and microelectronics through front companies and third countries. This industrial espionage was crucial for the Soviet Union to attempt to bridge the growing technology gap with the West, especially in personal computing and advanced digital systems. The sheer volume of information contained within a single microchip made its acquisition a potent form of a technological heist, offering a window into the advanced manufacturing capabilities and intellectual property of the West.
Conclusion
The Cold War’s secret technology heist was a pervasive and continuous aspect of the overarching geopolitical struggle. It was a shadowy war fought not with bullets and bombs, but with blueprints, algorithms, and the infiltration of minds. From the atomic bomb to stealth aircraft, each technological leap by one side spurred an intense effort by the other to either replicate, counter, or outright steal the innovation. The impact of these technological heists was profound, influencing strategic doctrines, accelerating arms races, and shaping the course of history for nearly half a century. Understanding this aspect of the Cold War provides a more complete picture of a conflict defined as much by clandestine acquisition as by overt policy. It underscores the perpetual drive for advantage, where knowledge itself was the ultimate prize.
WATCH NOW ▶️ SHOCKING: How The CIA Stole A Nuclear Submarine
FAQs
What was the Cold War secret technology heist?
The Cold War secret technology heist refers to covert operations during the Cold War era where intelligence agencies or spies stole advanced technology and classified information from rival nations to gain a strategic advantage.
Which countries were primarily involved in Cold War technology heists?
The United States and the Soviet Union were the primary countries involved, but other nations such as East Germany, the United Kingdom, and China also participated in espionage and technology theft during the Cold War.
What types of technology were targeted in these heists?
Technologies targeted included military hardware, nuclear weapons designs, aerospace advancements, cryptographic systems, and early computer technologies that could enhance defense capabilities.
How were these technology heists typically carried out?
Heists were conducted through espionage tactics such as recruiting spies, infiltrating research facilities, intercepting communications, and sometimes stealing physical prototypes or documents.
What impact did these technology heists have on the Cold War?
The theft of technology accelerated arms development and intelligence capabilities on both sides, intensifying the arms race and influencing diplomatic relations throughout the Cold War period.




