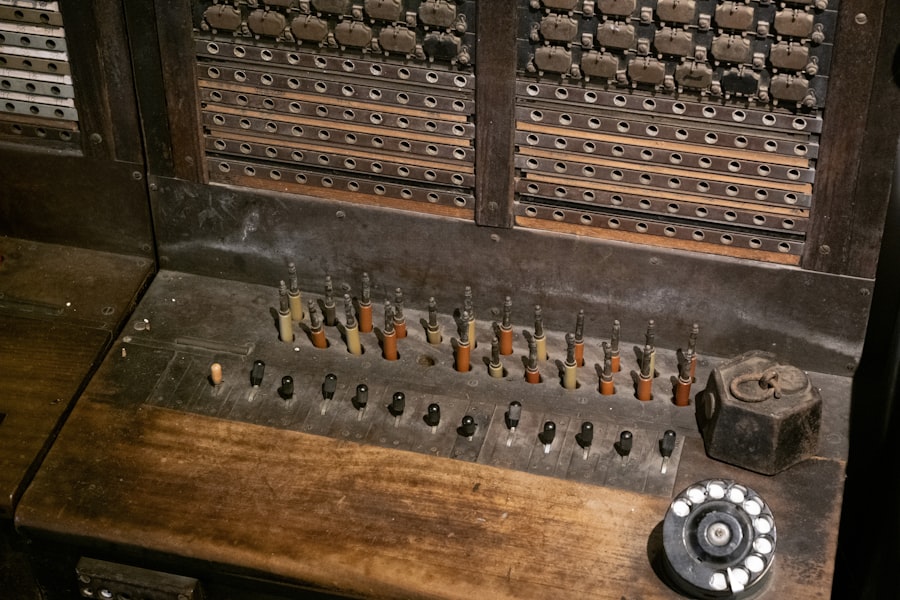
The KW-7 is a cryptographic device developed by the United States during the Cold War period for securing military and government communications. The machine operates using a rotor-based encryption system that processes classified information through mechanical components including rotors and electrical wiring circuits. This design builds upon principles established by earlier electromechanical cipher machines while incorporating enhanced security features for mid-20th century requirements.
The KW-7 was widely deployed across U.S. military branches and intelligence agencies for encrypting sensitive communications. Its mechanical construction provided operational durability in field conditions, making it suitable for various military applications where electronic equipment needed to function reliably in challenging environments.
With the advancement of computer-based encryption systems, the KW-7’s mechanical architecture presents limitations compared to modern digital cryptographic methods. Contemporary security assessments examine how legacy encryption devices like the KW-7 perform against current analytical techniques and computational capabilities. The transition from mechanical to digital encryption technologies reflects broader changes in cryptographic practices and the evolving requirements for protecting classified information in modern communication networks.
Key Takeaways
- The KW-7 encryption machine experienced a significant security breach impacting national security.
- Immediate actions and investigations were launched to address and attribute the compromise.
- The breach highlighted critical vulnerabilities and led to enhanced preventive measures.
- Collaboration with international allies was crucial in responding to the incident.
- Lessons learned are shaping the future outlook and improvements in encryption security.
Overview of the Security Breach
Recently, a significant security breach involving the KW-7 encryption machine has come to light, raising alarms within intelligence communities worldwide. Reports indicate that unauthorized access was gained to sensitive communications encrypted by the KW-7, potentially compromising classified information. The breach was discovered during routine security audits, which revealed anomalies in data transmission patterns that suggested external interference.
Initial investigations pointed to a sophisticated cyberattack, characterized by advanced techniques that bypassed traditional security measures. The breach not only exposed vulnerabilities within the KW-7 system but also highlighted the potential for adversaries to exploit these weaknesses for espionage or sabotage.
Potential Impact of the Compromise

The ramifications of the KW-7 breach are profound and multifaceted. First and foremost, the exposure of classified communications could jeopardize ongoing military operations and intelligence-gathering efforts. Sensitive information regarding troop movements, strategic plans, and diplomatic negotiations may have fallen into the hands of adversaries, undermining the effectiveness of national defense strategies.
Moreover, the breach raises concerns about the integrity of other encryption systems in use. If a machine as established as the KW-7 can be compromised, it casts doubt on the security of other legacy systems still in operation. This situation could lead to a crisis of confidence among intelligence agencies and military personnel, prompting a reevaluation of existing protocols and technologies used to protect sensitive information.
Actions Taken to Address the Breach
In response to the breach, immediate actions were initiated to contain the situation and mitigate further risks. Security teams were mobilized to conduct a thorough assessment of the KW-7 systems and identify any additional vulnerabilities that may have been exploited during the attack. This included a comprehensive review of operational protocols and encryption methodologies to ensure that all potential entry points were secured.
Additionally, communication channels were established with relevant stakeholders to inform them of the breach and its implications. This transparency was crucial in maintaining trust among allied nations and ensuring that collaborative efforts to address the situation were effective. The organization responsible for the KW-7 also began implementing enhanced security measures, including updated encryption algorithms and increased monitoring of data transmissions to detect any unusual activity.
Investigation and Attribution of the Breach
| Metric | Details |
|---|---|
| Device Name | KW-7 Encryption Machine |
| Type | Rotor-based encryption device |
| Period of Use | 1950s – 1970s |
| Compromise Date | Early 1960s |
| Compromise Method | Reverse engineering and cryptanalysis by NSA |
| Impact | Decryption of Soviet communications |
| Security Level | Considered moderate; vulnerable to cryptanalysis |
| Number of Rotors | 3 |
| Key Space | Approximately 10^15 possible keys |
| Known Weaknesses | Predictable rotor stepping and limited key changes |
The investigation into the breach was extensive, involving multiple agencies and cybersecurity experts tasked with uncovering the origins of the attack. Initial findings suggested that the breach was not merely an opportunistic hack but rather a coordinated effort by a state-sponsored actor with advanced capabilities. Digital forensics teams analyzed malware signatures and attack vectors to trace back to potential perpetrators.
Attribution in cyber incidents is notoriously complex, often requiring a combination of technical analysis and geopolitical context. As investigators delved deeper into the evidence, they began to identify patterns consistent with known threat actors. This process underscored the importance of international cooperation in cybersecurity efforts, as sharing intelligence and resources can significantly enhance the ability to attribute attacks accurately.
Lessons Learned from the Compromise
The KW-7 breach serves as a stark reminder of the evolving nature of cybersecurity threats and the necessity for continuous improvement in protective measures. One key lesson is the importance of regularly updating encryption technologies to counteract emerging threats. While the KW-7 has served its purpose well over decades, reliance on outdated systems can create vulnerabilities that adversaries are eager to exploit.
Furthermore, this incident highlights the need for comprehensive training programs for personnel involved in handling sensitive information. Ensuring that staff are aware of potential threats and equipped with knowledge about best practices in cybersecurity can significantly reduce risks associated with human error or negligence. The breach has prompted organizations to reassess their training protocols and invest in ongoing education for their teams.
Implications for National Security
The implications of the KW-7 breach extend beyond immediate operational concerns; they touch upon broader national security strategies. The incident raises questions about how nations protect their critical infrastructure and sensitive communications in an increasingly interconnected world. As adversaries become more adept at exploiting technological vulnerabilities, governments must prioritize cybersecurity as a fundamental component of national defense.
Moreover, this breach could lead to shifts in diplomatic relations as nations reassess their trust in shared intelligence systems. Countries may become more cautious about sharing sensitive information with allies if they perceive vulnerabilities in existing encryption technologies. This could result in a fragmented approach to intelligence sharing, ultimately hindering collaborative efforts to address global security challenges.
Repercussions for the Organization Responsible for the KW-7
The organization responsible for developing and maintaining the KW-7 faces significant repercussions following the breach. Public scrutiny has intensified as stakeholders demand accountability for lapses in security protocols that allowed unauthorized access to classified communications. This incident could lead to reputational damage, affecting future contracts and partnerships within both governmental and private sectors.
In addition to reputational risks, there may be legal ramifications stemming from the breach. If it is determined that negligence played a role in compromising sensitive information, affected parties may seek legal recourse against the organization. This situation underscores the critical importance of maintaining rigorous security standards and adhering to best practices in cybersecurity to avoid potential liabilities.
Steps Taken to Prevent Future Compromises
In light of the breach, proactive measures have been implemented to bolster security around the KW-7 encryption machine and similar systems. These steps include adopting more advanced encryption technologies that incorporate modern cryptographic principles designed to withstand contemporary cyber threats. By transitioning away from legacy systems where feasible, organizations can enhance their overall security posture.
Additionally, regular penetration testing and vulnerability assessments are now integral components of security protocols. These proactive measures allow organizations to identify weaknesses before they can be exploited by malicious actors. Furthermore, fostering a culture of cybersecurity awareness among personnel is essential; ongoing training programs are being developed to ensure that all staff members understand their role in safeguarding sensitive information.
Collaboration with Allies and Partners in Response to the Breach
Recognizing that cybersecurity is a collective challenge, collaboration with allies and partners has become paramount in addressing the implications of the KW-7 breach. Intelligence-sharing agreements are being strengthened to facilitate real-time information exchange regarding emerging threats and vulnerabilities. By working together, nations can develop more robust defenses against cyberattacks.
Joint exercises and training programs are also being organized to enhance preparedness among allied forces. These initiatives aim to create a unified response framework that can be activated in the event of future breaches or cyber incidents. Such collaboration not only improves individual nations’ security but also fosters trust among allies, reinforcing collective defense strategies.
Conclusion and Future Outlook for Encryption Security
The KW-7 encryption machine’s recent breach serves as a critical juncture in understanding the evolving landscape of cybersecurity threats. As technology continues to advance at an unprecedented pace, organizations must remain vigilant in adapting their security measures accordingly. The lessons learned from this incident will undoubtedly shape future approaches to encryption security, emphasizing innovation while addressing vulnerabilities inherent in legacy systems.
As adversaries become increasingly sophisticated in their tactics, governments must prioritize investment in cutting-edge technologies and collaborative efforts with international partners. By fostering a proactive cybersecurity culture and embracing innovation, nations can better safeguard their sensitive communications against future threats, ensuring that critical information remains secure in an ever-changing digital landscape.
The recent compromise of the KW-7 encryption machine has raised significant concerns regarding the security of classified communications. For a deeper understanding of the implications of this breach, you can read more about it in the article available on In The War Room. For further insights, check out this related article: In The War Room.
FAQs
What is the KW-7 encryption machine?
The KW-7 encryption machine was a cryptographic device used by the United States military during the Cold War to secure voice and data communications.
When was the KW-7 encryption machine developed and used?
The KW-7 was developed in the 1950s and saw extensive use throughout the 1960s and 1970s for secure military communications.
What does it mean that the KW-7 encryption machine was compromised?
Compromise of the KW-7 means that adversaries were able to break or bypass its encryption, potentially allowing them to intercept and understand classified communications.
How was the KW-7 encryption machine compromised?
The compromise typically involved cryptanalysis techniques, exploitation of operational errors, or technical vulnerabilities that allowed unauthorized parties to decrypt messages.
What were the consequences of the KW-7 compromise?
The compromise potentially exposed sensitive military communications, which could have jeopardized operational security and intelligence during the Cold War.
Were there any measures taken after the compromise of the KW-7?
Yes, following the compromise, the military upgraded to more secure encryption systems and improved operational security protocols to prevent similar breaches.
Is the KW-7 encryption machine still in use today?
No, the KW-7 has been retired and replaced by modern encryption technologies that offer stronger security.
Where can I learn more about the KW-7 encryption machine and its compromise?
Information can be found in declassified military documents, cryptographic history books, and academic research on Cold War communications security.




