Efficient Collection Management: Using Selectors
Efficient Collection Management: Using Selectors This article explores the critical role of selectors in the effective management of collections, whether they be physical libraries, digital archives, or curated lists of…
Understanding Second Party Third Party Exchange Rules
Second-party and third-party exchange rules are fundamental to the smooth functioning of many commercial and transactional environments. They define the boundaries and responsibilities when one entity interacts with another, not…
Title: The Future of Renewable Energy Dissemination formats metadata fields: – Topic: Renewable energy – Target audience: General public – Keywords: Renewable energy, sustainability, clean energy – Author: John Doe – Date: 10/15/2023 – Format: Article – Language: English
The future of renewable energy is a subject of intense global interest, driven by the twin imperatives of combating climate change and ensuring long-term energy security. As the world grapples…
Maximizing Efficiency with Automated Metadata Harvesting
Automated metadata harvesting, often unseen and unsung, serves as the silent engine driving operational efficiency across a multitude of digital landscapes. This process involves the automatic extraction and cataloging of…
Securing Network Memory: Host Logs and ARPA
The digital realm, much like a bustling city, relies on intricate networks for its operations. Within these networks, sensitive information flows like vital resources. Just as a city maintains records…
Enhancing Security with Access Control Lists and Socket Metadata
Access control lists (ACLs) and socket metadata represent foundational elements for bolstering network security. They function as sophisticated gatekeepers, meticulously governing which entities can interact with specific network resources and…
Menwith Hill: The Secret World of Satellite Dish Selectors
Menwith Hill: The Secret World of Satellite Dish Selectors Menwith Hill, nestled in the rolling Yorkshire Dales, is a facility shrouded in a persistent veil of mystery. While its imposing…
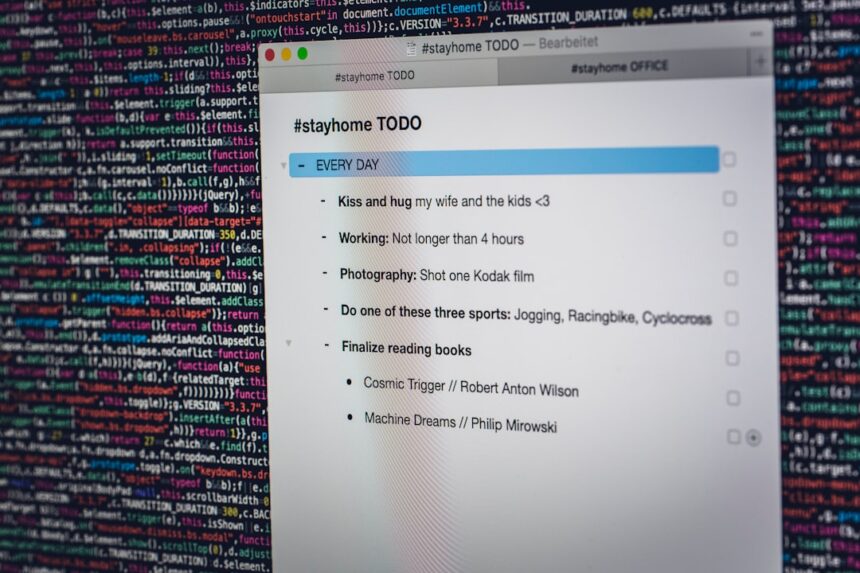
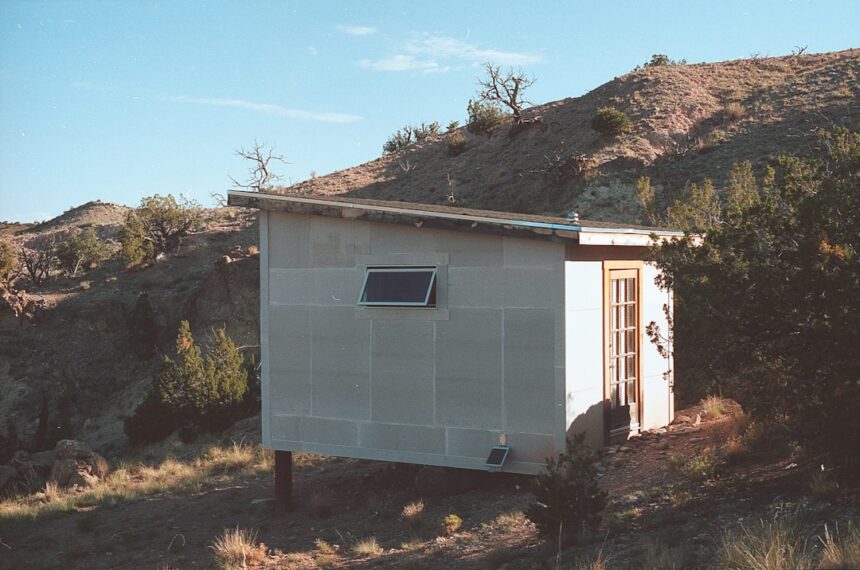
Securing Communications: Microwave Relay Intercept Shacks
Microwave relay systems, often forming the backbone of long-distance communication networks, possess a peculiar vulnerability: the need for physical structures to house the equipment. These structures, colloquially known as "shacks,"…
Telex Address Selector Tables: Efficient Communication Solutions
The ability to transmit information rapidly and reliably is a cornerstone of effective communication. In the era preceding widespread internet adoption, telex networks offered a crucial method for businesses and…
Meeting Carrier Compliance: CDR Retention Mandates
Maintaining compliance with Communications Data Retention (CDR) mandates is a critical operational and legal imperative for telecommunications carriers. These regulations, often established by governmental bodies, dictate the type and duration…