Strengthening US Nuclear Triad: Deterrent Strategies
The United States maintains a strategic nuclear triad—an interconnected system of land-based intercontinental ballistic missiles (ICBMs), submarine-launched ballistic missiles (SLBMs), and strategic bombers (including their bomber-carried nuclear weapons). This triad…
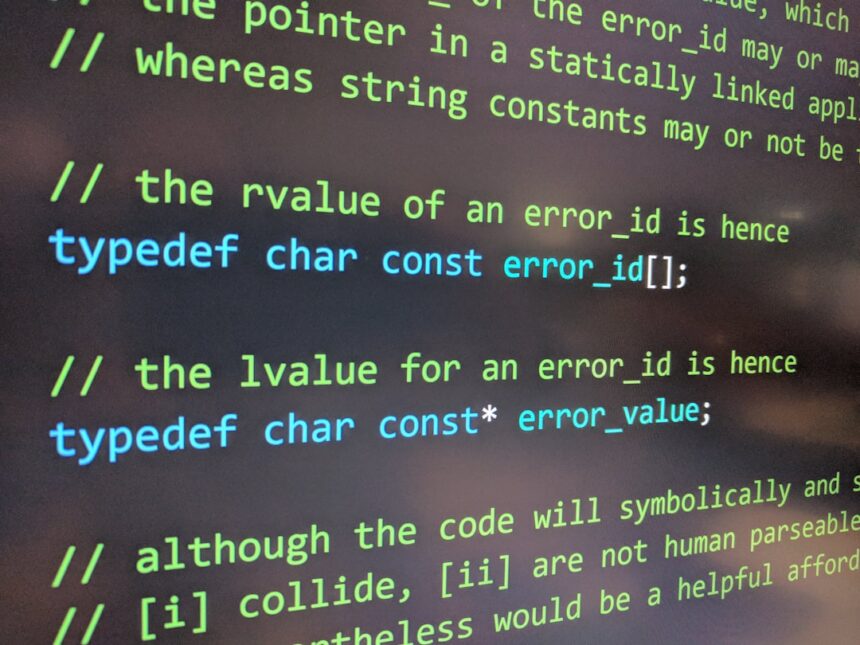
Identifying and Avoiding Department of Defense Metadata Traps
The effective management and utilization of digital information are critical for the Department of Defense (DoD). As reliance on data grows, so does the complexity of its handling. A significant,…
STANFINS Database Error: 37.7749° N, 122.4194° W
STANFINS Database Error: 37.7749° N, 122.4194° W A recent and unusual database error, flagged by the internal system as "STANFINS Database Error: 37.7749° N, 122.4194° W," has brought to light…
Diesel Generator Power Draw Tests: Ensuring Reliable Performance
Diesel Generator Power Draw Tests: Ensuring Reliable Performance The operation of modern infrastructure, from critical healthcare facilities to industrial manufacturing plants, relies heavily on a stable and consistent power supply.…
Maintaining Safety: Quarterly Filter Changes in Nuclear Silos
Maintaining Safety: Quarterly Filter Changes in Nuclear Silos The operational integrity and safety of nuclear silos are paramount. These facilities, designed to house and protect intercontinental ballistic missiles (ICBMs), represent…
Maintaining Safety: Quarterly Filter Changes in Nuclear Silos
Maintaining Safety: Quarterly Filter Changes in Nuclear Silos The operational integrity and safety of nuclear silos are paramount. These facilities, designed to house and protect intercontinental ballistic missiles (ICBMs), represent…
MILSTRIP and FEDLOG Data Leaks: A Security Concern
MILSTRIP and FEDLOG Data Leaks: A Security Concern The United States military and federal government rely on vast and intricate data management systems to maintain operational readiness and accountability. Among…
Metadata Wars: The Future of Warfare
The nature of conflict has always been shaped by technological advancement, and the current era is no exception. The battlefield has expanded beyond the physical to encompass the informational, and…
Decoy Signatures: Military Deception Tactics
Decoy signatures represent a cornerstone of military deception, a practice as old as warfare itself. Their fundamental purpose is to mislead an adversary regarding the true nature, location, or intent…
Strategic Watts: A New Approach to Painting
Strategic Watts: A New Approach to Painting The world of art, and specifically painting, is perpetually seeking innovation. Artists continually explore new techniques, materials, and conceptual frameworks to push the…