Secrets of Group Shadow War Choreography Revealed
The clandestine world of group shadow war choreography, a discipline rarely discussed beyond specialist circles, holds a certain mystique. It is a complex interplay of physiology, psychology, and spatial awareness,…
Jostle and Piperack: Radio Jamming Threat
The modern battlefield is a cacophony of electromagnetic signals. From the chatter of tactical radios to the guidance of precision munitions, the ether is a contested domain. Within this complex…
The Fatal Weakness of Military Checklists
Military checklists, lauded for their role in reducing errors and enhancing predictability in life-or-death situations, harbor a fundamental flaw that can undermine their efficacy. This inherent weakness lies not in…
Beacon Randomization: Too Late for Effective Security
The recent revelation of flaws within the widely adopted Beacon randomization protocols has ignited a spirited debate regarding the efficacy of current security measures in the face of evolving threats.…
Soviet OSINT Tradecraft Patterns: Uncovering Cold War Intelligence Techniques
The Soviet Union, a nation cloaked in a veil of secrecy throughout much of its existence, developed sophisticated methods for gathering intelligence. While often associated with covert operations and human…
The $2.4 Trillion Price Tag of the US Nuclear Arsenal
The United States maintains a vast and complex nuclear arsenal, a cornerstone of its national security strategy for decades. However, the sheer scale and ongoing modernization of this deterrent come…
Soviet Intelligence Monitors HVAC Cycles
The Soviet Union, a state historically characterized by its pervasive security apparatus and clandestine operations, employed a wide array of technical and human intelligence gathering methods. Among these, the monitoring…
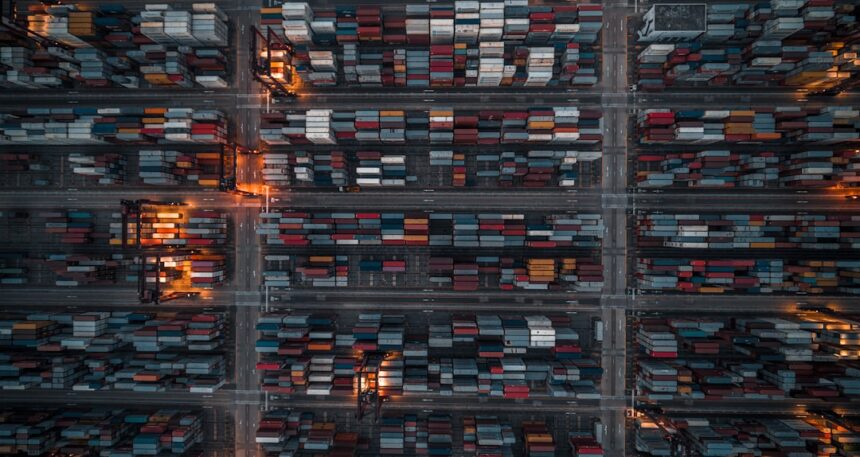
Pentagon Logistics: Metadata Glitch Impacts Operations
The Pentagon's vast logistical network, a complex web of supply chains, transportation routes, and inventory management crucial for global defense operations, recently experienced a significant disruption due to a metadata…
1980s Software Update and the Nuclear Threat
The 1980s, a decade often characterized by its vibrant cultural expressions and burgeoning technological advancements, also harbored a persistent and deeply unsettling undercurrent: the specter of nuclear war. Within this…
Strengthening US Nuclear Triad: Deterrent Strategies
The United States maintains a strategic nuclear triad—an interconnected system of land-based intercontinental ballistic missiles (ICBMs), submarine-launched ballistic missiles (SLBMs), and strategic bombers (including their bomber-carried nuclear weapons). This triad…