Preparing for Cyber Attacks: Hospital Power Draw Drill
The increasing reliance on digital infrastructure within healthcare organizations has inextricably linked…
The Unforgettable World: Metadata Fingerprints
Metadata, often an unseen yet pervasive element of digital information, functions as…
Ensuring Secure Data: Chain-of-Custody Partner Purge
In an era defined by the pervasive collection and utilization of digital…
National Security Authority Archive Exemptions: Protecting Classified Information
The safeguarding of classified information is a cornerstone of national security. Governments…
Legacy of Hard-Wired Guards: A Lasting Impact
The enduring influence of the "hard-wired" guard, a figure once ubiquitous in…
Turning a Leak into Bait: A Strategic Approach
The strategic manipulation of perceived vulnerabilities, often manifesting as "leaks," presents a…
Unveiling the Power of Amplify Decoy Codes Shadow Set
The Amplify Decoy Codes Shadow Set represents a sophisticated approach to digital…
Optimizing Warehouse Control System with Training
Optimizing Warehouse Control Systems with Effective Training The efficient operation of a…
Optimizing Climate Control Cycles with Load Signatures
Optimizing Climate Control Cycles with Load Signatures The efficient operation of climate…
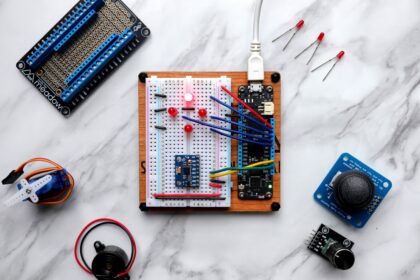
Creating Ideal Reptile Enclosures with Heat Mats and IR Sensors
Creating Ideal Reptile Enclosures with Heat Mats and IR Sensors The successful…