Analyzing Trawler Log Patterns for Undersea Cables
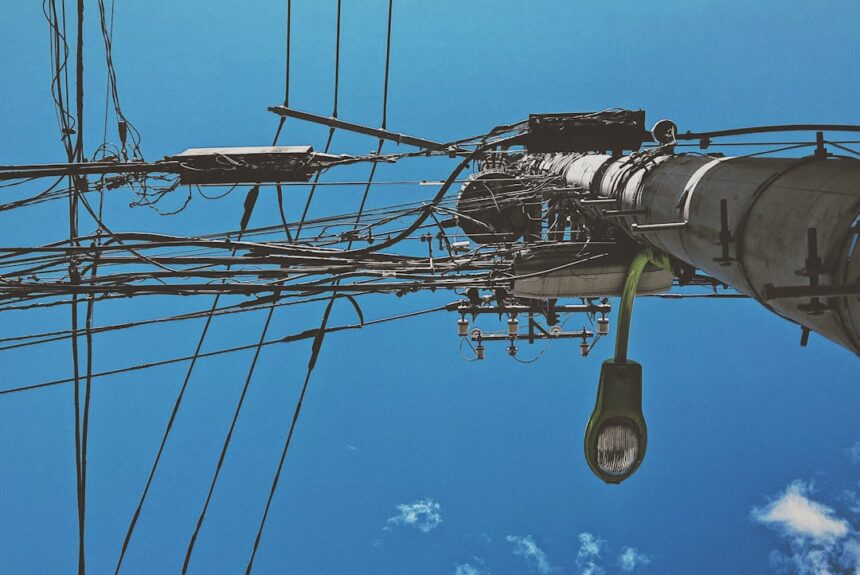
The intricate latticework of undersea cables forms the invisible nervous system of the modern world, facilitating global communication and data transfer. These vital arteries are not immune to the hazards of the marine environment, and among the most persistent threats are the activities of fishing trawlers. The deployment and operation of fishing gear, particularly bottom trawling, carries a significant risk of snagging and damaging these submerged assets. Understanding and mitigating this risk necessitates a detailed analysis of trawler log data, a process that can illuminate patterns of behavior and provide foresight into potential cable infringements.
Undersea cables, primarily fiber optic lines that carry vast amounts of data, are laid across the ocean floor in deliberate pathways known as cable routes. These routes are often established in areas with a history of maritime traffic and commercial fishing activity. The fishing industry, in turn, relies on the abundance of marine life found within these same oceanic territories. This confluence of interests, while economically vital, creates a delicate balance where the operational mechanics of one can inadvertently disrupt the integrity of the other.
Defining Demarcation: Cable Protection Zones and Operational Boundaries
A critical aspect of safeguarding undersea cables involves the establishment of Cable Protection Zones (CPZs). These are designated areas around known cable routes where certain maritime activities, including trawling, are restricted or prohibited. However, the effectiveness of these zones relies on accurate mapping, clear communication, and diligent enforcement. Trawler log data can reveal the extent to which these boundaries are respected and where potential conflicts may arise, acting as a seismograph for the subterranean tension between fishing fleets and cable infrastructure.
The Nature of the Threat: Trawling Mechanics and Cable Interaction
Bottom trawling involves dragging heavy nets across the seabed, designed to capture demersal (bottom-dwelling) fish species. The nets are often equipped with heavy doors, chains, and rollers to keep them open and to scour the seafloor. Unfortunately, these operational components can readily become entangled with submerged infrastructure, including the protective armor of undersea cables. The sheer force exerted by a trawler in these situations can cause significant damage, from superficial abrasions to complete severance of the cable, leading to costly repairs and widespread service disruptions. Even moderate snagging can compromise the cable’s protective layers, making it more vulnerable to future damage.
Recent studies have highlighted the significance of analyzing trawler log patterns for the protection and maintenance of undersea cables. Understanding these patterns can help in identifying potential risks and optimizing cable placement to minimize damage from fishing activities. For more insights on this topic, you can refer to a related article that discusses various aspects of undersea cable management and the impact of maritime activities on these crucial infrastructures. You can read more about it here: related article.
Deciphering Trawler Log Data: A Digital Rosetta Stone
Trawler logs, traditionally paper-based records maintained by fishing vessel captains, have increasingly transitioned to digital formats. These logs document a wealth of information pertaining to each fishing trip, including vessel identity, fishing grounds, duration of time spent at sea, types of gear deployed, and operational details such as deployment and retrieval times. When viewed through the lens of cable protection, these seemingly mundane records transform into a valuable repository of actionable intelligence. Like fragments of a lost language, deciphering these logs reveals the dialects of seabed engagement.
Granularity of Information: Essential Fields for Analysis
For effective analysis related to cable interference, specific fields within trawler logs are of paramount importance. These include:
- Vessel Identification and Type: Knowing the specific vessel and its class or size provides context for its operational capabilities and typical fishing grounds.
- Geographic Coordinates (Latitude/Longitude): Precise location data is crucial for overlaying fishing activity onto cable route maps. This allows for pinpointing instances where trawling occurred in proximity to, or directly over, cable pathways.
- Fishing Gear Description: The type of gear used (e.g., otter trawl, beam trawl, dredges) dictates the potential seabed contact and the severity of risk. Some gears are inherently more aggressive on the seabed than others.
- Start and End Times of Fishing Operations: These temporal markers are essential for understanding the duration of seabed contact and for correlating with any reported cable incidents.
- Depth of Operation: While not always explicitly recorded, the depth can be inferred from other data and is important for understanding the environmental context of fishing.
- Catch Data: While primarily for biological assessment, catch data can sometimes offer indirect clues about the type of seabed being fished.
Data Acquisition and Preprocessing: Laying the Foundation
The journey from raw trawler logs to insightful analysis begins with data acquisition. This can involve accessing national fisheries databases, receiving data directly from fishing companies, or even partnering with vessels that voluntarily share their digital logs. Once acquired, the data undergoes a crucial preprocessing phase. This involves cleaning the data to remove errors, inconsistencies, or missing values. Georeferencing is essential to ensure all spatial data is accurately mapped. Standardization of units and formats is also critical to allow for coherent comparison and analysis across different datasets. This phase is akin to preparing fertile soil before planting the seeds of understanding.
Navigational Data: The Unseen Hand in Trawler Movements
Modern fishing vessels are equipped with sophisticated GPS and navigation systems. The data generated by these systems, often recorded in Electronic Logbooks (ELBs) or Voyage Data Recorders (VDRs), provides an even more detailed account of a vessel’s movements than traditional log entries. This navigational data allows for the reconstruction of precise fishing tracks, identifying the exact path taken by the gear. Analyzing these tracks in relation to cable routes can reveal patterns of transgression and identify areas of high-risk overlap, acting as a compass pointing towards potential vulnerabilities.
Methodologies for Pattern Detection and Risk Assessment

The raw data, once cleaned and organized, becomes the raw material for analytical methodologies designed to uncover patterns indicative of cable interference risk. These methods range from simple spatial analysis to sophisticated machine learning algorithms.
Spatial Overlay and Proximity Analysis: Mapping the Danger Zones
The most fundamental analytical technique involves overlaying trawler activity data onto detailed maps of undersea cable routes. This allows for a direct visualization of fishing operations in relation to the cable infrastructure. Proximity analysis can then quantify the extent to which fishing occurred within a predefined buffer zone around cable routes. Identifying areas where fishing operations consistently overlap with cable pathways, especially specific types of trawling, highlights “hot spots” of potential risk. This is like surveying a battlefield to identify chokepoints and enemy staging areas.
Temporal Correlation with Incident Reports: Connecting the Dots
A critical step in validating analytical findings is to correlate identified fishing patterns with documented incidents of undersea cable damage. Trawler log data can reveal that specific vessels or fishing fleets were operating in a particular area shortly before or during the time a cable fault was reported. This temporal correlation, while not definitive proof of causation, provides strong circumstantial evidence and helps to refine risk assessments. It’s the detective work of linking observable actions to unforeseen consequences.
Statistical Modeling and Trend Identification: Forecasting Future Threats
Statistical models can be employed to identify trends and predict future risks. Analyzing historical trawler log data in conjunction with past cable damage records can reveal recurring patterns of activity that precede incidents. This might include increased trawling activity in specific seasons, in certain geographic locations, or by particular vessel types. These models can serve as early warning systems, allowing for proactive mitigation strategies to be implemented before damage occurs. This is akin to meteorology, predicting storms based on historical weather patterns.
Machine Learning for Anomaly Detection: Spotting the Unusual Suspects
Machine learning algorithms offer advanced capabilities for identifying unusual or anomalous trawling behavior. By training algorithms on typical fishing patterns, it is possible to flag instances where a vessel deviates significantly from its normal operational profile, especially if this deviation occurs near a cable route. Anomalies can also include sudden changes in fishing depth, unexpected detours, or prolonged periods of gear deployment in areas that are not typically fished. This is like a sophisticated alarm system that alerts you to a whisper in a crowded room.
Case Studies and Practical Applications: Learning from Experience
Examining real-world scenarios where trawler activity has intersected with undersea cables provides invaluable lessons. These case studies, when analyzed through the lens of trawler logs, demonstrate the practical utility of this data.
Documented Cable Strikes: Forensic Analysis of Log Data
In instances where cable strikes have occurred and been investigated, the associated trawler log data becomes a crucial piece of forensic evidence. By analyzing the logged positions, times, and gear types of vessels operating in the vicinity of the incident, investigators can often pinpoint the specific trawler responsible and the precise circumstances of the strike. This information is vital for attributing responsibility, calculating damages, and developing more effective prevention strategies. The log becomes a witness to the event, albeit a silent one.
Predictive Modeling for Proactive Cable Protection: Visualizing the Future
Advanced analysis of trawler logs can move beyond reactive incident investigation to proactive risk prediction. By building predictive models that forecast areas and times of heightened risk, cable operators can implement targeted measures. This might include intensified monitoring, deploying warning buoys, or collaborating with fishing authorities to raise awareness and encourage alternative fishing grounds. The goal is to shift from extinguishing fires to preventing them from starting.
Collaborative Efforts: Bridging the Gap Between Fisheries and Cable Operators
The most effective use of trawler log analysis often involves collaborative efforts between the fishing industry, cable operators, and regulatory bodies. Sharing anonymized and aggregated log data can provide a comprehensive picture of fishing activity and its potential impact on subsea infrastructure. This collaboration can lead to the development of mutually beneficial solutions, such as integrated mapping platforms that display both cable routes and fishing restrictions, fostering a shared responsibility for protecting these vital assets.
Recent studies have highlighted the significance of analyzing trawler log patterns to enhance the protection of undersea cables, which are crucial for global communications. A related article discusses the implications of these patterns on cable maintenance and security, emphasizing the need for better monitoring techniques. For more insights on this topic, you can read the article here: undersea cable security. Understanding these patterns not only aids in safeguarding vital infrastructure but also contributes to the overall resilience of maritime operations.
Challenges and Future Directions: Navigating the Ethical and Technical Landscape
| Metric | Description | Typical Values | Relevance to Undersea Cables |
|---|---|---|---|
| Trawler Pass Frequency | Number of trawler passes recorded per square kilometer | 0 – 15 passes/month | Indicates potential risk zones for cable damage due to fishing activity |
| Average Trawling Speed | Speed at which trawlers operate during fishing | 3 – 5 knots | Helps estimate the force and impact on cables if dragged over |
| Depth of Trawling | Depth range where trawling nets are deployed | 50 – 400 meters | Critical for assessing cable vulnerability based on cable depth |
| Net Width | Width of the trawling net used | 20 – 50 meters | Determines the area of seabed impacted per trawling pass |
| Seasonal Variation | Changes in trawling activity by season | Higher in summer months, lower in winter | Important for scheduling cable maintenance and monitoring |
| Distance from Shore | Typical distance trawlers operate from coastline | 5 – 50 nautical miles | Helps map high-risk zones relative to cable routes |
| Reported Cable Incidents | Number of cable faults attributed to trawling activity | Varies by region, typically 1-5 incidents/year | Direct measure of impact on undersea cable infrastructure |
While the analysis of trawler log data offers significant promise for undersea cable protection, several challenges remain. Addressing these challenges will be crucial for maximizing the effectiveness of these analytical approaches.
Data Privacy and Security Concerns: Respecting the Captain’s Confidentiality
Fisheries data, including trawler logs, can contain commercially sensitive information about fishing grounds and catch volumes. Ensuring the privacy and security of this data is paramount. Robust anonymization techniques and strict access control measures are necessary to build trust and encourage data sharing, while still allowing for effective analysis. The right to privacy is a crucial anchor in this data-driven sea.
Data Standardization and Interoperability: Building Bridges Between Systems
The diverse nature of trawler log formats, often varying by vessel, region, and reporting system, presents a significant hurdle for interoperability. Developing standardized data formats and protocols will be essential for enabling seamless integration and analysis of data from multiple sources. Without this, we are trying to read several different books written in different languages without a translator.
Technological Advancements: Harnessing the Power of Big Data and AI
Advancements in big data analytics and artificial intelligence offer exciting opportunities for enhancing trawler log analysis. Exploring the application of AI-powered pattern recognition, predictive analytics, and even computer vision for analyzing trawl camera footage could lead to more sophisticated and accurate risk assessments. This is the advent of more powerful sonar, capable of detecting subtle shifts in the underwater currents of behavior.
Policy and Regulatory Frameworks: Establishing Clear Guidelines for Coexistence
Effective analysis of trawler log data must be supported by robust policy and regulatory frameworks. Clear guidelines on reporting requirements, enforcement mechanisms for cable protection zones, and collaborative data-sharing agreements are essential. Policy decisions, informed by data analysis, can create a more predictable and safer environment for both fishing and cable operations. This is the framing of the rules of engagement to ensure a peaceful coexistence.
In conclusion, the analysis of trawler log patterns is an indispensable tool for understanding and mitigating the risks posed to undersea cables by fishing activities. By treating these logs as a rich source of data, applying rigorous analytical methodologies, and fostering collaborative partnerships, we can navigate the complex seascape of maritime activity and subsea infrastructure, ensuring the continued flow of global connectivity. This process transforms a potential source of conflict into a beacon of foresight, illuminating the path toward a more secure and interconnected future.
FAQs
What are trawler log patterns in the context of undersea cables?
Trawler log patterns refer to the recorded paths and activities of fishing trawlers, which are analyzed to understand their movements and potential interactions with undersea cables. These patterns help in assessing risks to cable infrastructure from fishing operations.
Why is it important to study trawler log patterns for undersea cables?
Studying trawler log patterns is important because fishing trawlers can inadvertently damage undersea cables through their nets and equipment. Understanding these patterns helps in planning cable routes, implementing protective measures, and reducing the risk of cable faults.
How are trawler log patterns collected and analyzed?
Trawler log patterns are collected using vessel monitoring systems (VMS), automatic identification systems (AIS), and fishing logs. The data is then analyzed using geographic information systems (GIS) and other mapping tools to identify frequent fishing areas and potential conflict zones with undersea cables.
What measures can be taken to protect undersea cables from trawler activities?
Protective measures include routing cables away from high-traffic fishing areas, burying cables deeper beneath the seabed, installing protective coverings, and establishing exclusion zones or fishing restrictions near cable routes to minimize the risk of damage.
Are there international regulations regarding fishing near undersea cables?
Yes, international regulations such as those under the International Cable Protection Committee (ICPC) and various maritime laws encourage cooperation between cable operators and fishing communities. These regulations aim to protect undersea cables by managing fishing activities in sensitive areas and promoting awareness among fishermen.