The revelation that the KL-47 encryption machine, a cornerstone of secure communication for numerous governmental and military entities, has been compromised represents a seismic event in the world of information security. This breach, which has been carefully kept under wraps until now, exposes a vulnerability of profound implications, casting a long shadow over decades of classified transmissions and potentially undermining the foundational trust in digital privacy for a significant portion of the global intelligence apparatus. The scale of the compromise is still being fully assessed, but early indications suggest that adversaries have gained access to encrypted communications that were believed to be impenetrable, opening a Pandora’s Box of historical and ongoing secrets. The ramifications are not merely academic; they translate directly into real-world consequences, impacting national security, diplomatic relations, and the very integrity of covert operations.
The KL-47, a product of a bygone era of cryptographic design, was once lauded as a paragon of digital security. Developed and deployed during a period when computational power was considerably less ubiquitous and sophisticated than it is today, it represented the cutting edge of its time. Its underlying architecture, while innovative for its era, also bears the hallmarks of the technological constraints and theoretical understandings of its inception. To comprehend the gravity of its compromise, one must first understand what the KL-47 was designed to do and how it operated.
Historical Context of the KL-47’s Development
The genesis of the KL-47 can be traced back to a specific geopolitical climate, an era of heightened tensions and the burgeoning importance of secure communication in espionage and warfare. The drive to create an encryption device that could withstand the increasing analytical capabilities of rival nations was paramount. This period saw a dedicated effort from cryptographers and engineers to build a machine that would be resistant to known decryption techniques.
The Cold War Arms Race in Cryptography
The Cold War, a protracted period of geopolitical tension between the United States and the Soviet Union and their respective allies, fostered an intense arms race, not just in conventional weaponry, but also in the clandestine realm of code-making and code-breaking. Each side sought to gain an advantage through superior intelligence gathering, and a critical component of this was the ability to both encrypt their own communications and decipher those of their adversaries. The KL-47 emerged within this crucible, a product of the urgent need to maintain communication security amidst a constant threat of interception.
Technological Constraints and Design Philosophies of the Era
The technological landscape of the mid to late 20th century dictated significant design choices in cryptographic systems. The processing power of computers was nascent, and the understanding of complex mathematical principles that underpin modern encryption was still evolving. Cryptographic designs of this period often relied on intricate mechanical systems synchronized with digital components, aiming for a level of complexity that was intended to overwhelm contemporary cryptanalytic efforts. The KL-47, with its specific algorithms and operational procedures, was a direct product of these limitations and the prevailing design philosophies.
Operational Principles of the KL-47
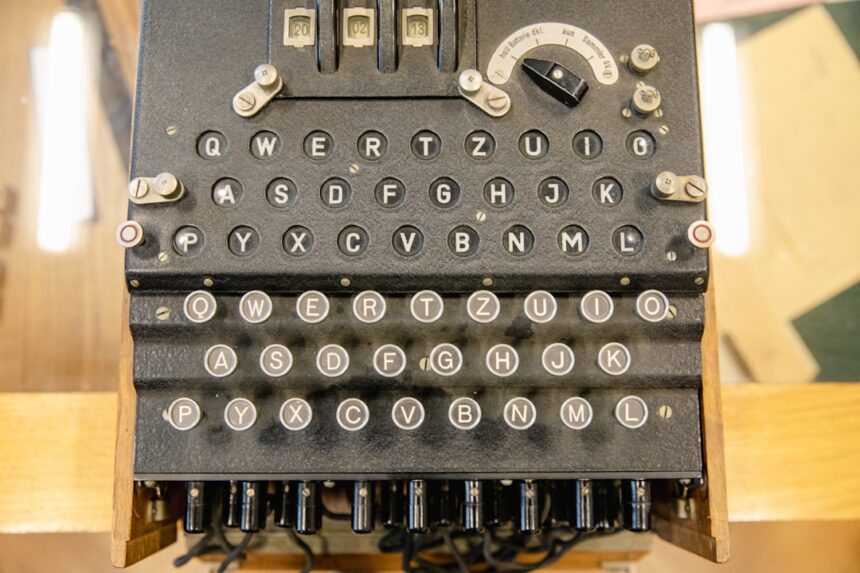
At its core, the KL-47 employed a sophisticated system of rotor-based encryption, a well-established principle at the time, but one that was implemented with a unique and proprietary approach. The machine’s complexity was intended to create an astronomical number of possible keystream permutations, making brute-force attacks infeasible. The system relied on a combination of internal wiring, rotor stepping mechanisms, and operational procedures to generate the ciphertext.
Rotor-Based Encryption Mechanisms
The KL-47 utilized a series of rotating wheels, or rotors, each with a unique internal wiring pattern. When a character was input, an electrical signal would pass through the rotors, undergoing a series of substitutions and transpositions. The stepping of these rotors, often influenced by the input character and the state of previous rotors, created a constantly changing cipher alphabet. The number of rotors, their initial configuration, and the specific wiring within each rotor contributed to the overall multiplicative complexity of the encryption.
Key Management and Operational Procedures
Beyond the physical mechanisms of the machine, the effective security of the KL-47 was heavily reliant on rigorous key management protocols and strict adherence to operational procedures. The “key” in this context referred to the initial settings of the rotors and any other parameters that determined the encryption process for a given communication session. These keys were typically generated manually and distributed through secure channels. The failure to maintain the secrecy of these keys, or lapses in operational discipline, could render the most sophisticated encryption algorithm vulnerable.
The recent compromise of the KL-47 encryption machine has raised significant concerns regarding the security of classified communications. For a deeper understanding of the implications and potential vulnerabilities associated with this incident, you can read a related article that discusses the broader context of encryption technology and its challenges in modern warfare. Check it out here: IntheWarRoom.
The Nature of the KL-47 Compromise
The breach of the KL-47 is not a simple matter of an adversary finding a stray key or exploiting a minor software bug. Instead, the evidence points towards a more fundamental and deeply unsettling vulnerability that has been exploited, rendering a significant portion of its encrypted communications susceptible to decryption. The nature of this compromise suggests a sophisticated and sustained effort on the part of the adversaries.
Exploitation of Algorithmic Weaknesses
Cryptographic algorithms, like any complex system, can harbor subtle weaknesses. These weaknesses are often not apparent at first glance and may only be discovered through extensive cryptanalysis, advanced computational resources, or a deep understanding of the underlying mathematical principles. The compromise of the KL-47 appears to stem from the exploitation of such inherent algorithmic flaws. The sophistication of the attack suggests adversaries who possessed both the theoretical knowledge and the computational power to uncover these vulnerabilities.
Identification of Hidden Patterns and Biases
Through meticulous observation and sophisticated analytical tools, adversaries may have identified subtle, non-random patterns or biases within the ciphertext generated by the KL-47. These patterns, even if statistically insignificant to casual observation, can serve as critical footholds for cryptanalysts. The existence of these biases suggests that the machine’s output was not as random or unpredictable as its designers had intended, creating a discernible trail that could be followed.
Advanced Cryptanalytic Techniques
The successful decryption of communications encrypted by the KL-47 indicates the deployment of advanced cryptanalytic techniques. This could include methods such as differential cryptanalysis, linear cryptanalysis, or even novel approaches developed specifically to target the KL-47’s unique architecture. The application of these advanced techniques implies a dedicated, multi-faceted approach by the adversaries, likely involving significant computational resources and considerable human expertise.
Potential for Both Historical and Real-Time Decryption
The implications of this compromise are twofold: the ability to decrypt past communications and the potential to intercept and decrypt current transmissions. The access to historical data, even if decades old, can provide invaluable insights into past decisions, strategies, and secrets. More alarmingly, if the vulnerability persists and is actively being exploited today, it means that current sensitive communications are also at risk.
Retroactive Decryption of Past Communications
The compromise opens the door to decrypting a vast trove of historical communications. This could include diplomatic cables, intelligence reports, military orders, and other sensitive information that has remained classified for decades. The potential for unearthed secrets is immense, with implications for understanding past conflicts, geopolitical maneuvers, and the motivations of various actors on the world stage. It is akin to finding a master key that unlocks a vault of forgotten histories.
Ongoing Interception and Decryption Capabilities
The most chilling aspect of the KL-47 compromise is the potential for ongoing interception and decryption. If the exploit remains active and the adversaries have not been deterred, then any entity still relying on the KL-47 for secure communication is currently broadcasting their secrets in plain text to those who hold the decryption key. This poses an immediate and existential threat to current operations and national security.
The Discovery and Investigation

The process by which this compromise was uncovered has been a protracted and covert affair. The revelation to the public has been carefully managed, highlighting the sensitivity of the information and the ongoing efforts to mitigate the damage. The investigation itself has been a monumental undertaking, spanning multiple agencies and requiring a level of expertise rarely deployed in such situations.
The Initial Signs of Vulnerability
The earliest indications of a problem were likely subtle, perhaps a consistent anomaly in decrypted intercepted messages or a statistically improbable success rate in breaking a small sample of KL-47 encrypted communications. These initial signs, like faint whispers in a storm, would have been enough to trigger a deep dive by security analysts.
Anomalies in Intercepted Communications
Security analysts are trained to look for deviations from the norm. In this case, anomalies in intercepted communications that were processed through decryption algorithms might have been the first red flags. These could manifest as patterns that defied expected statistical distributions or a persistent inability to reconcile certain decoded messages with known events.
Cryptanalytic Breakthroughs in Controlled Environments
The eventual confirmation of the KL-47’s weakness would have come through significant cryptanalytic breakthroughs achieved in controlled environments. This would have involved dedicated teams of experts, utilizing advanced computing power and novel analytical techniques to systematically dismantle the encryption.
The Covert Investigation Process
Once a potential vulnerability was identified, the investigation would have immediately shifted to a highly classified and covert operation. The goal would be to confirm the compromise, identify the extent of the breach, and understand the methods employed by the adversaries without tipping them off to the investigation.
Multi-Agency Task Force Formation
Confirming and addressing a breach of this magnitude would necessitate the formation of a dedicated task force, bringing together experts from various intelligence agencies, cybersecurity firms, and potentially academic institutions. This collaborative effort ensures a comprehensive approach, leveraging diverse skill sets and perspectives.
Attribution and Extent of the Breach
A critical phase of the investigation involves attempting to attribute the compromise to specific actors. This means identifying who is responsible and how they managed to achieve this feat. Simultaneously, efforts are made to ascertain the full extent of the breach – which communications have been compromised, over what period, and by whom. This is akin to assessing the full damage after an earthquake.
Ramifications and Consequences

The compromise of the KL-47 encryption machine sends shockwaves through the global intelligence community and beyond. The consequences are far-reaching, impacting national security, international relations, and the trust placed in secure communication systems. The long-term repercussions are still unfolding, but the immediate aftermath is already significant.
Impact on National Security and Intelligence Operations
For nations that relied on the KL-47, this breach represents a critical blow to their national security infrastructure. The compromised communications could expose sensitive intelligence, tactical plans, and the identities of individuals operating in clandestine roles.
Exposure of Sensitive State Secrets
The most direct consequence is the potential exposure of state secrets. Information that was deemed sensitive enough to warrant encryption by a supposedly secure machine could now be in the hands of adversaries, leading to geopolitical instability, compromising ongoing operations, and potentially jeopardizing lives.
Compromise of Covert Agent Networks
Covert agents and their handlers rely on secure communication channels for their safety and the success of their missions. If these channels are compromised, the identities of agents, their directives, and their operational methods could be revealed, leading to their capture, interrogation, or worse. This is like seeing the blueprints of a spy network laid bare.
Erosion of Trust in Encrypted Communications
The KL-47 was considered a reliable workhorse for secure communications for decades. Its compromise erodes the fundamental trust that governments and organizations place in such systems, creating a period of profound uncertainty and forcing a rapid reassessment of security protocols.
Accelerated Adoption of Newer Cryptographic Standards
In the wake of this revelation, there will be an unprecedented push to transition to newer, more robust encryption algorithms and protocols. The KL-47’s failure serves as a stark reminder that even seemingly impenetrable systems can eventually be outmaneuvered.
Increased Scrutiny of Legacy Systems
This incident will undoubtedly lead to increased scrutiny of all legacy cryptographic systems still in use. Organizations will be compelled to conduct thorough audits and risk assessments of their existing encryption infrastructure to identify and mitigate similar vulnerabilities before they can be exploited.
The recent compromise of the KL-47 encryption machine has raised significant concerns about the security of classified communications. This incident highlights the vulnerabilities that can exist even in advanced encryption technologies. For a deeper understanding of the implications of such breaches, you can read a related article that discusses the broader impact on national security and intelligence operations. Check it out here to explore the potential consequences and the steps being taken to mitigate these risks.
Mitigation and Future Safeguards
| Metric | Details |
|---|---|
| Machine Name | KL-47 |
| Type | Encryption Machine |
| Country of Origin | United States |
| Period of Use | 1950s – 1970s |
| Compromise Date | Late 1960s |
| Compromise Method | Cryptanalysis and Intelligence Gathering |
| Impact | Decryption of Soviet Communications |
| Security Weakness | Predictable Key Settings and Mechanical Vulnerabilities |
| Countermeasures | Upgraded Encryption Machines and Improved Key Management |
The immediate priority following the discovery of the KL-47 compromise is to contain the damage and implement measures to prevent future occurrences. This involves not only addressing the specific vulnerabilities of the KL-47 but also reinforcing the broader principles of cryptographic security.
Decommissioning and Replacement of KL-47 Systems
The most obvious and immediate step is the complete decommissioning and discontinuation of the use of KL-47 encryption machines. Any reliance on these systems, even with attempts at re-securing them, would be a grave mistake in light of the confirmed compromise.
Phased Rollout of Secure Replacements
The transition to secure replacements will be a complex and phased process. Newer, quantum-resistant cryptographic algorithms and more modern hardware will be essential. This rollout will require significant investment in infrastructure, training, and rigorous testing to ensure the integrity of the new systems.
Immediate Secure Communication Protocols
While new systems are being introduced, urgent measures will be put in place to ensure secure communication through alternative, verified channels. This might involve leveraging existing, more secure networks or employing temporary, high-assurance communication methods.
Enhancing Cryptographic Research and Development
This incident underscores the perpetual nature of the cat-and-mouse game between cryptographers and adversaries. A renewed focus on fundamental research and development in cryptography is essential to stay ahead of evolving threats.
Investment in Quantum-Resistant Cryptography
The advent of quantum computing poses a future threat to many current encryption algorithms. This compromise highlights the need for accelerated research and development into quantum-resistant cryptography, ensuring that future communication systems can withstand the computational power of emerging technologies.
Fostering International Collaboration in Cryptographic Standards
Establishing and maintaining robust cryptographic standards requires international collaboration. Sharing knowledge, best practices, and threat intelligence can help create a more unified and resilient global cybersecurity posture. This is like building a collective shield against unseen attackers.
The compromise of the KL-47 encryption machine serves as a stark and urgent wake-up call. It is a potent reminder that in the ever-evolving landscape of cybersecurity, complacency is the greatest threat. The secrets once locked away by what was believed to be an impenetrable barrier have been exposed, necessitating a profound reevaluation of our defenses and a renewed commitment to the art and science of cryptography. The lessons learned from this breach will undoubtedly shape the future of secure communication for years to come.
FAQs
What is the KL-47 encryption machine?
The KL-47 is a cipher device used by the United States military during the Cold War era to encrypt and decrypt classified communications. It was designed to provide secure voice and data transmission.
What does it mean that the KL-47 encryption machine was compromised?
A compromise of the KL-47 encryption machine means that adversaries were able to gain unauthorized access to its encryption methods or keys, potentially allowing them to intercept and decode sensitive communications.
How was the KL-47 encryption machine compromised?
The compromise typically involved espionage activities, such as the theft of key materials, reverse engineering, or exploitation of operational weaknesses, though specific details may vary depending on historical accounts.
What were the consequences of the KL-47 compromise?
The compromise could have led to the exposure of classified military communications, undermining operational security and giving adversaries strategic advantages during conflicts or intelligence operations.
How was the security of encryption machines like the KL-47 improved after such compromises?
Following compromises, security measures were enhanced by developing more advanced encryption algorithms, improving key management protocols, increasing physical security, and implementing stricter operational procedures to prevent future breaches.