Survival Tactics: Electronic Warfare and Signal Masking
The modern battlefield is a symphony of electromagnetic signals. Communication, navigation, targeting, and even the operation of critical infrastructure all rely on the invisible but powerful waves that permeate our environment. For individuals or groups operating in hostile or contested territories, understanding and mastering electronic warfare (EW) and signal masking techniques is not merely an advantage; it is a fundamental requirement for survival. This article explores essential tactics and principles for evading or disrupting enemy electronic surveillance and strike capabilities.
The electromagnetic spectrum, often referred to as the “fifth domain” of warfare, encompasses all forms of electromagnetic radiation. From radio waves used for communication to visible light and even gamma rays, each segment of the spectrum possesses unique properties and applications. In the context of survival, the most frequent concern revolves around radio frequency (RF) and microwave bands, which are exploited for a vast array of military and civilian functions.
Radio Frequency (RF) Bands
RF waves are utilized for a multitude of purposes, including voice and data communication, radar detection, remote sensing, and wireless networking. Understanding the specific frequencies employed by adversaries is crucial for effective evasion. Different frequency bands have varying propagation characteristics, influencing their range, susceptibility to interference, and the types of antennas required for transmission or reception.
Low Frequency (LF) and Medium Frequency (MF)
These lower frequency bands tend to have longer wavelengths, allowing them to penetrate obstacles and travel over longer distances, often following the curvature of the Earth. While less common for high-bandwidth data transmission, they are still utilized for certain types of communication and broadcasting. Their larger antenna requirements can sometimes make them more detectable.
High Frequency (HF)
HF bands (3-30 MHz) are known for their ability to bounce off the ionosphere, enabling intercontinental communication. This characteristic, while beneficial for long-range clandestine operations, also means signals can be intercepted by a wide range of receivers. Understanding ionospheric conditions is key to predicting HF radio propagation.
Very High Frequency (VHF) and Ultra High Frequency (UHF)
VHF (30-300 MHz) and UHF (300 MHz-3 GHz) are the workhorses for many modern military and civilian communication systems. They offer wider bandwidths and are more line-of-sight dependent, making them generally more susceptible to jamming and detection by direction-finding equipment. This is where sophisticated encryption and spread spectrum techniques become vital for secure communication.
Microwave Bands
Microwave frequencies (typically above 1 GHz) are used for high-bandwidth data transmission, satellite communications, radar systems, and wireless local area networks. Their directional nature and high frequencies allow for precise targeting but also make them susceptible to blockage and interference from physical objects.
Radar Systems
Radar operates by transmitting electromagnetic pulses and analyzing the reflected echoes. These systems are used for target detection, tracking, and navigation. Understanding radar frequencies, pulse repetition intervals (PRIs), and antenna scanning patterns can inform strategies for evasion and masking.
Satellite Communications (SATCOM)
SATCOM relies on geostationary or low-earth orbit satellites to relay signals globally. While offering extensive coverage, SATCOM terminals can be relatively fixed and their transmissions can be powerful and detectable.
In the realm of modern military strategy, electronic warfare and signal masking play crucial roles in ensuring survival and operational effectiveness. A related article that delves deeper into these topics can be found at In the War Room, which explores the intricacies of how electronic countermeasures can protect assets and enhance situational awareness on the battlefield. Understanding these concepts is vital for military personnel and strategists alike, as they navigate the complexities of contemporary warfare.
Signal Detection and Interception
The foundation of EW defense lies in understanding how signals are detected and intercepted. Adversaries employ a diverse array of tools and techniques to identify, locate, and analyze electromagnetic emissions. Recognizing these threats is the first step in mitigating them.
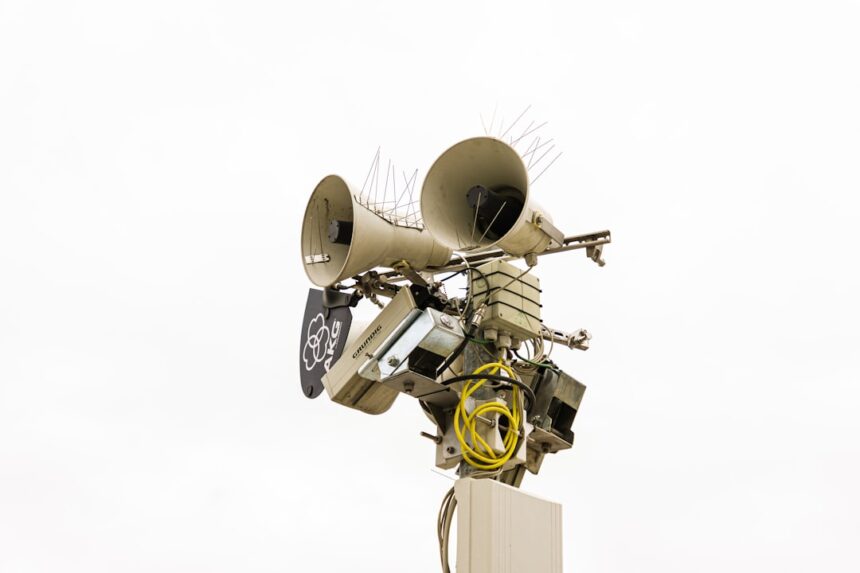
Radio Direction Finding (RDF)
RDF systems are designed to determine the direction of an incoming radio signal. Portable and vehicle-mounted RDF units can triangulate a transmitter’s location by taking bearings from multiple points. Sophisticated systems can even estimate distance based on signal strength and other parameters.
Monopulse and Amplitude-Comparison RDF
These are common RDF techniques that rely on comparing the phase or amplitude of a signal received by different elements of an antenna array. This allows for precise bearing determination.
Interferometric RDF
This method measures the difference in phase of a signal arriving at different points on an antenna array. It offers high accuracy, particularly at longer distances.
Signal Intelligence (SIGINT)
SIGINT is the broad category of intelligence derived from the interception and analysis of electromagnetic signals. It encompasses both electronic intelligence (ELINT), which focuses on non-communication signals like radar, and communications intelligence (COMINT), which deals with intercepted communications.
Electronic Intelligence (ELINT)
ELINT involves analyzing parameters like frequency, pulse width, pulse repetition frequency, antenna scan rate, and power output of radar and other electronic systems. This information can reveal the type of system, its operational mode, and its intended purpose.
Communications Intelligence (COMINT)
COMINT involves intercepting and analyzing voice or data transmissions. Without proper security measures, these transmissions can reveal tactical information, troop movements, and operational plans.
Passive Sensors
Many modern detection systems are passive, meaning they do not emit their own signals, making them difficult to detect. These include sensitive receivers capable of picking up faint signals from great distances and advanced signal processing capabilities to analyze them.
Signal Analyzers and Spectrum Analyzers
These instruments are used to dissect and understand the characteristics of intercepted signals. They can identify modulation types, bandwidths, and other parameters that can be used for identification and tracking.
Signal Masking and Minimization Techniques

Effective signal masking aims to reduce or eliminate the detectability of an individual or group’s electronic presence. This involves a combination of minimizing emissions, obscuring them, and employ counter-detection measures.
Emission Control (EMCON)
EMCON is a strict doctrine of controlling all electromagnetic emissions. It involves shutting down all non-essential electronic devices and only activating them when absolutely necessary, and then only for the shortest possible duration.
Scheduled Transmissions
If communications are unavoidable, they should be conducted on a pre-arranged schedule using narrow time windows. This allows adversaries to anticipate and potentially target these slots, but it reduces the overall time a signal is active.
Short Burst Transmissions
Transmitting data in very short, high-speed bursts can make interception and location more difficult. The rapid nature of the transmission can overwhelm less sophisticated detection equipment.
Frequency Hopping and Spread Spectrum
These techniques reduce the probability of a signal being intercepted or jammed. Frequency hopping involves quickly changing the transmission frequency across a wide band according to a pseudo-random pattern. Spread spectrum techniques distribute the signal energy over a much wider frequency range, making it appear as low-level background noise to non-synchronized receivers.
Pseudo-Random Noise (PRN) Codes
Sophisticated encryption often employs PRN codes to determine the hopping sequence or spreading pattern. Only receivers synchronized with the correct code can decode the signal.
Direct Sequence Spread Spectrum (DSSS)
In DSSS, the data signal is multiplied by a much higher data rate “chipping” sequence. This spreads the signal energy over a wide band, making it resistant to narrowband jamming and interference.
Antenna Design and Placement
The type and placement of antennas significantly influence signal detectability. Directional antennas can focus transmissions in a specific direction, reducing outward radiation, while omnidirectional antennas broadcast in all directions.
Low-Profile and Concealed Antennas
Using antennas that are small, integrated into existing structures, or disguised as inconspicuous objects can reduce visual detection.
Shielding and Faraday Cages
Physical shielding, such as using Faraday cages or conductive materials, can block or attenuate electromagnetic radiation, both for incoming signals and outgoing transmissions.
Electronic Countermeasures (ECM)

ECM refers to actions taken to prevent or reduce an enemy’s effective use of the electromagnetic spectrum. This can include jamming, deception, and spoofing.
Jamming
Jamming involves transmitting interfering signals to disrupt enemy communications or radar. This can be achieved through various methods, from simple noise generators to sophisticated techniques that mimic the characteristics of the targeted signal.
Barrage Jamming
This is a broad-spectrum jamming technique that floods a wide range of frequencies with noise, attempting to overwhelm all communication channels. Its effectiveness is often limited by power requirements and the ability to cover all relevant frequencies.
Spot Jamming
Spot jamming focuses jamming energy on a specific frequency or narrow band used by the adversary. This is more efficient than barrage jamming, provided the target frequencies are known.
Deceptive Jamming
Deceptive jamming aims to confuse the enemy by transmitting false signals designed to mislead their targeting or navigation systems. This could involve creating ghost targets on radar or broadcasting false instructions.
Deception and Spoofing
Deception aims to mislead the enemy into making incorrect decisions by presenting false or misleading information through the electromagnetic spectrum. Spoofing involves impersonating a legitimate signal source to gain access to systems or transmit false data.
Radar Deception
This can involve techniques like corner reflectors or radar chaff to create false radar targets, drawing enemy attention or fire away from actual locations.
GPS Spoofing
By broadcasting counterfeit GPS signals, an adversary could trick navigation systems into believing they are in a different location. This can lead to misdirection or even deliberate targeting of friendly forces.
In the realm of modern military strategy, understanding electronic warfare and signal masking is crucial for survival in hostile environments. The ability to disrupt enemy communications while protecting one’s own signals can be the difference between success and failure in combat situations. For a deeper insight into these tactics and their implications, you can explore a related article on this topic at In the War Room, which discusses the evolving nature of warfare and the importance of technological advancements in maintaining an edge over adversaries.
Intelligence Gathering and Situational Awareness
| Metrics | Data |
|---|---|
| Electronic Warfare Techniques | Jamming, spoofing, and deception |
| Signal Masking Technologies | Frequency hopping, spread spectrum, and low probability of intercept |
| Survival in Electronic Warfare Environment | Effective use of electronic countermeasures and stealth technologies |
| Impact on Communication Systems | Disruption of radio, radar, and GPS signals |
Survival in an EW-contested environment hinges on continuous intelligence gathering and maintaining a high level of situational awareness regarding the electromagnetic landscape.
Passive Listening and Signal Monitoring
Maintaining a constant passive listening posture allows for the detection of enemy emissions without revealing one’s own presence. This can provide vital information about enemy activity, locations, and intentions.
Spectrum Monitoring Tools
Utilizing spectrum analyzers and other monitoring equipment can help identify active transmissions, their frequencies, and their characteristics. This allows for the creation of an “electromagnetic picture” of the operational area.
Threat Assessment and Prioritization
Not all detected signals represent an immediate threat. Understanding the capabilities of enemy EW systems and the significance of their emissions is crucial for prioritizing countermeasures and allocation of resources.
Identifying High-Value Targets
Enemy command and control (C2) nodes, early warning radar systems, and precision-guided munitions guidance systems are typically high-value targets for EW operations. Detecting and disrupting these can have a significant impact.
Maintaining Operational Security (OPSEC)
OPSEC is the process of protecting information that could be exploited by adversaries. In EW, this extends to all aspects of electronic activity, from the selection of equipment to the procedures for its use.
Avoiding Electronic Signatures
Every electronic device leaves a signature. Minimizing these signatures through careful planning and disciplined execution of EMCON and masking techniques is paramount.
Adversary EW Capabilities Assessment
Continuously assessing and updating knowledge of adversary EW capabilities, including their equipment, doctrine, and training, is essential for adapting survival tactics. This might come from HUMINT, SIGINT, or reconnaissance.
In conclusion, survival in an environment saturated with electromagnetic signals requires a proactive and informed approach to electronic warfare and signal masking. By comprehending the intricacies of the spectrum, understanding detection methods, implementing rigorous masking techniques, employing effective countermeasures, and maintaining superior intelligence and situational awareness, individuals and groups can significantly enhance their chances of operating undetected and surviving in contested territories. This is not a static field; continuous learning and adaptation to evolving threats and technologies are as critical as the fundamental principles themselves.
FAQs
What is electronic warfare?
Electronic warfare refers to the use of the electromagnetic spectrum to attack or defend against an adversary. It includes activities such as electronic jamming, electronic deception, and electronic masking.
What is signal masking in the context of survival?
Signal masking in survival refers to the techniques used to hide or protect electronic signals from detection or interference by hostile forces. This can include methods such as using camouflage, encryption, or frequency hopping.
Why is electronic warfare and signal masking important in survival situations?
In survival situations, electronic warfare and signal masking are important for maintaining communication and information security. By protecting electronic signals from detection or interference, individuals or groups can avoid being located or targeted by hostile forces.
What are some common electronic warfare and signal masking techniques used in survival situations?
Common techniques include using low-power transmissions, employing frequency agility, utilizing directional antennas, and employing encryption to protect communications from interception or jamming.
How can individuals prepare for electronic warfare and signal masking in survival situations?
Individuals can prepare by learning about electronic warfare and signal masking techniques, practicing secure communication methods, and having the necessary equipment such as encrypted radios and signal masking devices. Additionally, understanding the local electromagnetic environment and potential threats can help in preparing for survival situations.