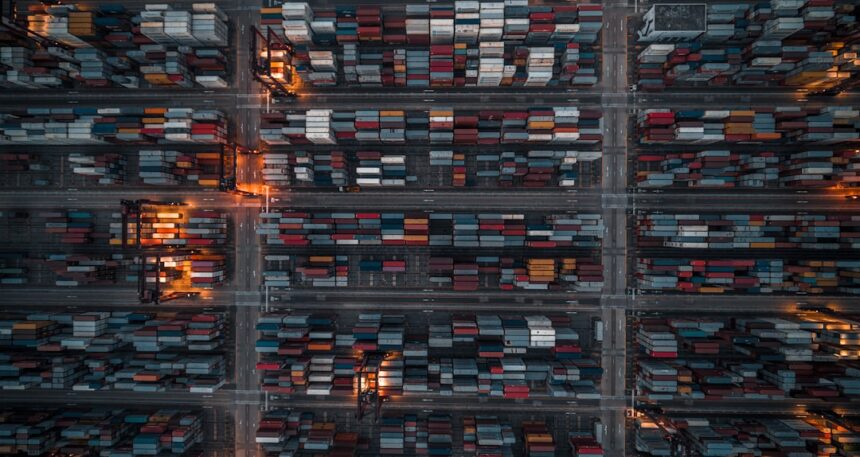
The Pentagon’s vast logistical network, a complex web of supply chains, transportation routes, and inventory management crucial for global defense operations, recently experienced a significant disruption due to a metadata glitch. This seemingly minor technical anomaly cascaded into tangible operational impacts, highlighting the vulnerabilities inherent in digitally reliant systems within even the most secure government institutions.
The origin of the disruption lay not in the physical movement of goods or the integrity of the data itself, but in the descriptive information about that data. Metadata, often referred to as “data about data,” provides context, definition, and classification. In a system as intricate as Pentagon logistics, metadata dictates how information is categorized, retrieved, relayed, and ultimately acted upon.
What is Metadata in a Logistics Context?
Within the Pentagon’s logistical framework, metadata encompasses a wide array of information. This includes, but is not limited to:
- Item Identification: Unique serial numbers, part numbers, stock keeping units (SKUs), and their associated descriptions, manufacturers, and approved usage.
- Location Data: Geographic coordinates, warehouse identifiers, depot codes, and specific shelving or bin locations for stored equipment and supplies.
- Transportation Details: Vehicle types, capacity, routes, transit times, fuel consumption rates, and carrier information.
- Status Updates: Real-time information on the progress of shipments, inventory levels, requisition status, maintenance schedules, and operational readiness.
- Regulatory Compliance: Classification of items, hazardous material designations, export/import controls, and security clearance requirements.
- Ownership and Custodianship: Information regarding which unit or organization is responsible for specific assets.
The Technical Mechanism of the Glitch
While specific technical details remain classified, the core issue is understood to have involved corrupted or misaligned metadata fields. This could have manifested in several ways:
Incorrect Data Tagging
One avenue for the glitch was the erroneous tagging of logistical assets. For example, a batch of sensitive electronic components might have been mistakenly tagged with metadata indicating they were mundane office supplies, or vice versa. This would lead to misrouting, inappropriate storage conditions, or delays in processing due to incorrect security protocols.
Hierarchical Data Structure Errors
Logistical data is often organized in hierarchical structures to facilitate complex queries and analysis. A glitch in the metadata defining these relationships could have severed connections between related pieces of information. A supply requisition, for instance, might not have been properly linked to the corresponding inventory item it was intended to draw from.
Timestamp or Versioning Inconsistencies
In systems that track the lifecycle of assets and operations, accurate timestamps and version control are paramount. A metadata glitch involving these elements could have rendered historical data unreliable or prevented the accurate identification of the most current specifications or operational requirements.
Data Transformation Anomalies
During the transfer or processing of data between different logistical systems, metadata often undergoes transformations. A bug in these transformation algorithms could have introduced errors, misinterpreting or corrupting the descriptive attributes of the logistical data.
The recent Pentagon logistics metadata glitch has raised significant concerns about data security and operational efficiency within the Department of Defense. For a deeper understanding of the implications of this incident, you can read a related article that explores the broader context of military logistics and data management challenges at In The War Room. This article delves into how such glitches can impact military readiness and the importance of robust data systems in modern defense operations.
Operational Repercussions Across the Supply Chain
The consequences of the metadata glitch were not theoretical; they manifested as tangible disruptions across various facets of Pentagon logistics, impacting the seamless flow of resources necessary for global operations.
Disrupted Inventory Management
The most immediate and widespread impact was on inventory management. Systems responsible for tracking stock levels, identifying surplus, and managing replenishment became unreliable.
Inaccurate Stock Counts
With corrupted metadata, the system might have reported higher or lower quantities of items than were actually present. This led to situations where requisitions were placed for items believed to be in stock but were not, or where valuable resources were overlooked because their metadata indicated they were depleted.
Inefficient Stock Rotation and Maintenance
The metadata often dictates the shelf-life of perishable goods, the maintenance schedules for equipment, and the optimal rotation of inventory. Glitches in these fields could have led to items expiring or requiring maintenance going unnoticed, or conversely, to unnecessary maintenance on equipment that was still in good condition.
Challenges in Asset Tracking and Auditing
Auditing and accountability are critical in military logistics. The metadata glitch made it difficult to accurately trace the movement and status of assets, complicating both internal audits and external accountability measures.
Transportation and Deployment Delays
The seamless movement of personnel and materiel is a cornerstone of military readiness. The metadata glitch created friction points within the transportation and deployment systems.
Misrouting of Shipments
One of the most direct impacts was the misrouting of critical shipments. If the metadata for a particular shipment contained incorrect destination codes or transportation preferences, the goods could have been sent to the wrong location, causing significant delays and necessitating complex rerouting efforts.
Inaccurate Load Planning and Optimization
Logistics planners rely heavily on metadata to optimize cargo loads, select appropriate transportation modes, and calculate transit times. Corrupted metadata could have led to inefficient load planning, resulting in underutilized capacity, increased transportation costs, and extended delivery times.
Communication Breakdowns with Third-Party Carriers
A significant portion of military logistics relies on contracted civilian carriers. The metadata glitch likely hampered effective communication and information exchange with these partners, as the data fields they relied upon for tracking and scheduling may have been inaccurate or unreadable.
Impact on Readiness and Operational Support
Ultimately, the disruptions in inventory and transportation directly affected the Pentagon’s ability to support active military operations and maintain readiness levels around the globe.
Shortages of Critical Supplies
In regions where supply chains are already stretched thin, even minor disruptions can lead to shortages of essential items, from ammunition and spare parts to medical supplies and rations. The metadata glitch exacerbated these vulnerabilities.
Delayed Deployment of Equipment and Personnel
The timely deployment of forces and equipment is essential for responding to emerging threats. Delays caused by logistical hiccups directly impacted this ability, potentially affecting the effectiveness of military responses.
Increased Operational Costs
Addressing the aftermath of the metadata glitch involved significant resource allocation. Rerouting shipments, conducting manual inventory checks, and rectifying data errors all incurred considerable costs in terms of personnel time, fuel, and administrative overhead.
The Underlying Causes and Contributing Factors

While the metadata glitch itself was the proximate cause of the operational impacts, its occurrence points to broader systemic vulnerabilities and contributing factors within the Pentagon’s digital infrastructure.
Complexity of Integrated Systems
The Pentagon operates a vast ecosystem of interconnected logistical systems. These systems, often developed over decades and acquired from different vendors, are designed to integrate to provide a holistic view of operations. However, the sheer complexity of these integrations can create numerous points of failure.
- Interoperability Challenges: Ensuring seamless data flow and understanding between disparate systems is a perpetual challenge. Metadata standards may not be uniformly applied or interpreted across all platforms.
- Legacy Systems: The continued reliance on older, legacy systems, while sometimes necessary for backward compatibility, can introduce vulnerabilities when integrated with modern, more sophisticated platforms. These older systems may have less robust metadata management capabilities.
- Data Silos: Despite efforts towards integration, data silos can persist. If metadata is not consistently updated or synchronized across all relevant silos, discrepancies are inevitable.
Human Factors and Process Gaps
Technology is only one part of the equation; human factors and established processes play an equally crucial role in the effective management of digital systems.
- Training and Awareness: Insufficient training or a lack of awareness regarding the criticality of metadata management can lead to errors during data entry, updates, or system maintenance.
- Manual Data Entry Errors: While many processes are automated, some still rely on manual data entry. Even small typographical errors in metadata can have cascading effects.
- Insufficient Validation Protocols: Inadequate validation protocols for metadata can allow erroneous data to enter the system without being flagged for correction. This includes checks for data consistency, format, and adherence to predefined rules.
Cybersecurity Considerations
While the metadata glitch was not initially characterized as a direct cyberattack, it underscores the intertwined nature of cybersecurity and data integrity.
- Vulnerability to Insider Threats: Malicious or accidental actions by individuals with privileged access can lead to data corruption, including metadata.
- Exploitable System Flaws: Sophisticated adversaries could potentially identify and exploit vulnerabilities in the metadata management systems to disrupt operations, even without directly stealing sensitive information.
- Ransomware and Malware: While unlikely in this specific instance, advanced malware or ransomware could target metadata databases, rendering critical logistical information inaccessible.
Remediation and Recovery Efforts

The Pentagon’s response to the metadata glitch involved a multifaceted approach to identify the root cause, mitigate immediate impacts, and implement measures to prevent recurrence.
Immediate Containment and Data Integrity Checks
The initial priority was to halt the spread of the corrupted metadata and assess the extent of the damage.
- Isolation of Affected Systems: Technicians likely isolated the specific systems or databases where the metadata corruption was detected to prevent further propagation.
- Data Backups and Restoration: The organization would have relied on its data backup protocols to restore affected information from known good states. This process can be time-consuming and carries the risk of data loss if backups are not up-to-date.
- Manual Verification: In many cases, manual verification of critical logistical data would have been necessary to confirm its accuracy and integrity after restoration.
Root Cause Analysis and System Audits
A thorough investigation into the genesis of the glitch was paramount to inform future preventive measures.
- Forensic Analysis of System Logs: Technicians would have meticulously reviewed system logs, audit trails, and error reports to pinpoint the exact sequence of events that led to the metadata corruption.
- Code Review and Software Audits: If the glitch was traced to a specific software component or algorithm, extensive code reviews and software audits would be conducted to identify the underlying bug.
- Process Review: An examination of existing data management processes, including data entry, validation, and update procedures, would have been initiated to identify any procedural weaknesses that contributed to the issue.
Long-Term Preventive Measures and System Enhancements
Beyond immediate fixes, the Pentagon is obligated to implement long-term strategies to bolster its logistical data infrastructure.
- Metadata Standardization Initiatives: The implementation or reinforcement of robust metadata standards across all logistical systems is crucial. This includes defining consistent data formats, naming conventions, and validation rules.
- Enhanced Data Validation and Quality Assurance: Strengthening automated data validation checks and establishing more rigorous quality assurance protocols for metadata can prevent erroneous data from entering the system.
- Investment in Advanced Data Management Tools: The Pentagon may need to invest in more sophisticated data management platforms that offer advanced capabilities for metadata tracking, version control, and anomaly detection.
- Regular System Updates and Patching: Ensuring all software and hardware components are regularly updated and patched is a fundamental aspect of cybersecurity and system stability, which indirectly protects metadata integrity.
- Cross-Training and Knowledge Sharing: Fostering a culture of comprehensive training and knowledge sharing among personnel responsible for data management can improve awareness and reduce the likelihood of human error.
Recently, the Pentagon faced a significant challenge due to a logistics metadata glitch that raised concerns about the accuracy of military supply chain data. This incident highlights the importance of robust data management systems in defense operations. For a deeper understanding of the implications of such glitches, you can read more in this insightful article on military logistics and technology advancements at In the War Room. The article delves into how technology can both aid and complicate military logistics, emphasizing the need for continuous improvement in data integrity.
Lessons Learned and Future Preparedness
| Date | Issue | Impact |
|---|---|---|
| May 15, 2021 | Logistics metadata glitch | Delayed shipments, inaccurate tracking |
| May 20, 2021 | Recovery efforts | Resumed normal operations, data cleanup |
| May 25, 2021 | Lessons learned | Improved data validation processes |
The metadata glitch serves as a potent reminder of the fragility of complex digital infrastructures and the imperative for continuous vigilance. The lessons drawn from this incident will undoubtedly inform future strategic decisions regarding the Pentagon’s logistical capabilities.
The Interdependence of Digital and Physical Logistics
This incident underscores that in modern warfare and global operations, digital infrastructure is not merely a support function but an integral component of physical logistics. Any weakness in the digital realm has direct and tangible consequences for the movement of goods and the readiness of forces.
The Importance of Data Governance and Management
The glitch highlights that robust data governance frameworks, encompassing policies, procedures, and accountability for data quality, are not optional but essential for operational resilience. Effective data management extends beyond mere data storage; it involves the meticulous stewardship of data about data.
The Need for Continuous System Modernization and Agility
The Pentagon’s logistical systems are constantly challenged by evolving threats and operational demands. A static approach to technology and infrastructure is insufficient. Continuous modernization, embracing agile development methodologies, and fostering a culture of adaptability are critical for maintaining operational effectiveness.
Proactive Risk Assessment and Mitigation
The incident should spur a deeper and more proactive approach to risk assessment within the logistical domain. This includes identifying potential metadata vulnerabilities, simulating failure scenarios, and developing comprehensive mitigation strategies before they manifest as operational disruptions.
Strengthening Cybersecurity Posture for Data Integrity
While the glitch may not have been a direct cyberattack, the incident reinforces the need to integrate cybersecurity considerations into all aspects of data management. Protecting metadata from unauthorized access, modification, or deletion is as vital as safeguarding the underlying logistical data itself.
In conclusion, the Pentagon’s metadata glitch, while a technical anomaly, has had significant and far-reaching operational impacts. It serves as a critical case study, emphasizing the paramount importance of meticulous data management, robust system architecture, and a proactive approach to cybersecurity in maintaining the logistical backbone of global defense operations. The lessons learned are essential for ensuring future preparedness and resilience in an increasingly interconnected and digitalized world.
FAQs
What is the Pentagon logistics metadata glitch?
The Pentagon logistics metadata glitch refers to a technical issue within the Pentagon’s logistics system that resulted in inaccurate or missing metadata for critical supplies and equipment.
How did the Pentagon logistics metadata glitch impact operations?
The glitch impacted operations by causing delays in the delivery of supplies and equipment, as well as creating challenges in tracking and managing inventory.
What caused the Pentagon logistics metadata glitch?
The specific cause of the Pentagon logistics metadata glitch has not been publicly disclosed. However, it is believed to be a technical issue within the logistics system that led to errors in metadata management.
What steps are being taken to address the Pentagon logistics metadata glitch?
The Pentagon is working to address the glitch by conducting a thorough review of the logistics system and implementing measures to improve metadata accuracy and management.
What are the potential implications of the Pentagon logistics metadata glitch?
The potential implications of the glitch include disruptions to military operations, increased costs associated with supply chain management, and potential risks to national security.