Microwave relay systems, often forming the backbone of long-distance communication networks, possess a peculiar vulnerability: the need for physical structures to house the equipment. These structures, colloquially known as “shacks,” are not mere sheds. They are the nerve centers of the relay, the guardians of the signal as it leaps from one tower to the next. Understanding the security of these microwave relay intercept shacks is paramount for national security, corporate integrity, and the very flow of information that underpins modern society. This article delves into the multifaceted nature of securing these critical nodes.
The Purpose and Function of Microwave Relay Shacks
At their core, microwave relay shacks are engineered to house sensitive electronic equipment essential for the transmission and reception of microwave signals. These signals, traveling in focused beams, require precise alignment and amplification as they bridge vast geographical distances. The shacks serve as both a protective enclosure and a stable platform for the parabolic antennas and associated electronics. Imagine them as the stoic guardians standing watch at strategic points, ensuring the message does not falter on its journey. They are the silent sentinels, indispensable links in the chain of communication. Their design prioritizes environmental protection, from harsh weather conditions such as extreme temperatures, precipitation, and wind, to electromagnetic interference that could corrupt the signal.
Components Within a Relay Shack
Inside a typical microwave relay shack, one will find a carefully orchestrated assembly of technology. This includes:
Key Electronic Components:
- Transceivers: These devices both transmit and receive the microwave signals. They are the vocal cords and ears of the relay.
- Amplifiers: As signals weaken over distance, amplifiers boost their strength, ensuring clarity and reach. These are the bellows that lend power to the voice.
- Modulators and Demodulators: These units convert digital data into analog signals suitable for microwave transmission and vice versa. They are the translators, converting between different languages of information.
- Waveguides and Coaxial Cables: These conduits carry the microwave signals to and from the antennas, acting as the arteries of the system.
- Power Supplies: Reliable and often redundant power sources are crucial to maintain continuous operation. Without power, the sentinel slumbers.
- Monitoring and Control Systems: These systems oversee the performance of the equipment, detect faults, and allow for remote management. They are the watchful eyes and responsive hands of the operation.
Ancillary Infrastructure:
Beyond the core electronics, shacks also house essential supporting infrastructure:
- Environmental Control Units (ECUs): Air conditioning and heating systems maintain optimal operating temperatures, preventing equipment failure due to heat or cold.
- Surge Protectors and Grounding Systems: These are vital for protecting the delicate electronics from electrical surges caused by lightning or power fluctuations. They act as the grounding rod, dissipating destructive energy.
- Backup Power Systems: Generators or battery banks provide uninterrupted power in the event of a mains failure. These are the reserve forces, ready to step in when the primary lines are cut.
The Strategic Placement of Relay Shacks
The location of these shacks is not arbitrary; it is dictated by the physics of microwave propagation and the topography of the land. Microwave signals travel in straight lines, like lasers, and are easily blocked by obstacles.
Line-of-Sight Propagation:
The fundamental principle governing microwave communication is line-of-sight (LOS). This means that for effective transmission, there must be an unobstructed path between the transmitting antenna and the receiving antenna. Relay shacks are strategically placed on high ground, hilltops, or tall structures to achieve this LOS, often facilitated by the towers to which they are connected.
Topographical Considerations:
Planners meticulously analyze terrain maps, elevation data, and potential obstructions such as mountains, buildings, and dense vegetation. The ideal placement minimizes the need for excessively tall towers, which are more expensive to construct and maintain, and more vulnerable to environmental stress.
Network Design and Connectivity:
The placement of shacks also takes into account the overall network topology, ensuring seamless connectivity and redundancy. In many cases, multiple shacks form a chain, with each relaying the signal to the next. The failure of a single shack can disrupt a significant portion of the network, highlighting the importance of their security.
Microwave relay intercept shacks have played a crucial role in intelligence gathering, particularly during the Cold War era. For a deeper understanding of the historical significance and operational methods of these intercept stations, you can explore a related article that delves into their impact on modern surveillance techniques. To read more about this fascinating topic, visit this article.
The Adversarial Landscape: Threats to Relay Shacks
The critical nature of microwave relay shacks makes them attractive targets for a range of malicious actors, from state-sponsored espionage to opportunistic criminals. Understanding these threats is the first step in building effective defenses.
Espionage and Intelligence Gathering
State actors are perpetually seeking to intercept or disrupt the communications of adversaries. Microwave relay shacks offer a direct conduit into sensitive information flows.
Signal Interception:
The microwave beams themselves can be intercepted by sophisticated equipment positioned within range of the relay. This allows adversaries to eavesdrop on telephone calls, data transmissions, and other forms of communication. It is akin to placing an ear against a wall to listen to private conversations.
Jamming and Disruption:
Beyond eavesdropping, adversaries may seek to intentionally disrupt communications by emitting signals that interfere with the microwave frequencies. This “jamming” can render the relay inoperable, creating communication blackouts for the target. This is the equivalent of shouting loudly in a crowded room, drowning out all other voices.
Technological Superiority:
Nations with advanced technological capabilities may develop specialized equipment designed to exploit specific vulnerabilities in microwave systems, such as directional antennas or techniques to bypass encryption at the physical layer.
Vandalism and Sabotage
Beyond the realm of sophisticated espionage, microwave relay shacks are also vulnerable to more straightforward acts of vandalism and sabotage, often driven by lower-level motivations.
Intentional Damage:
Opportunistic vandals may target shacks to cause destruction, graffiti, or theft of valuable equipment. While seemingly less sophisticated, the cumulative effect of such damage can be significant, disrupting critical infrastructure.
Targeted Industrial Sabotage:
In competitive industries, rivals may resort to sabotage to gain an advantage, disrupting a competitor’s communication capabilities during critical business periods or events. This can have severe financial repercussions.
Disruption of Critical Infrastructure:
In certain geopolitical contexts or during periods of unrest, shacks might be targeted as symbols of authority or as a means to disrupt essential services, impacting public safety, emergency response, and economic activity.
Environmental and Accidental Threats
While not malicious, natural phenomena and human error can pose significant threats to the integrity of relay shacks.
Extreme Weather Events:
Hurricanes, tornados, heavy snowfall, and severe winds can physically damage the shacks and their antennas, leading to prolonged outages. These are the unpredictable furies of nature, against which robust construction is the only defense.
Wildlife Interference:
Birds nesting on antennas or in ventilation systems, or rodents gnawing on cables, can cause malfunctions. While seemingly minor, these can cumulatively disrupt operations.
Human Error and Maintenance Issues:
Improper installation, inadequate maintenance, or accidental damage during repair work can introduce vulnerabilities or lead to equipment failure. The human element, even with the best intentions, can be a source of unforeseen problems.
Physical Security Measures: The Fortifications of Information

Given the diverse threats, robust physical security of microwave relay shacks is a non-negotiable prerequisite for secure communications. This involves a layered approach, building defenses from the ground up.
Perimeter Security: The First Line of Defense
The immediate surroundings of a relay shack are the first opportunity to deter unauthorized access.
Fencing and Barriers:
Secure, well-maintained fencing is the most basic and essential perimeter defense. This can include chain-link fencing, anti-climb coatings, and robust gates. The fence acts as a clear signal of ownership and a physical impediment.
Access Control Points:
Controlled entry points are crucial. Gates should be locked and accessible only to authorized personnel. Security patrols or remote monitoring of these points can further enhance security.
Warning Signage:
Clear and prominent signage indicating private property, restricted access, and potential hazards can serve as a deterrent and inform legitimate visitors of protocols.
Shack Construction and Hardening
The structure of the shack itself is a critical element of its security.
Robust Building Materials:
Shacks should be constructed from durable materials that can withstand attempted forced entry, vandalism, and extreme weather. Reinforced concrete, steel, and tamper-proof locking mechanisms are essential.
Tamper-Resistant Doors and Windows:
Doors should be solid-core, reinforced, and fitted with high-security locks. Windows, if present, should be minimal, small, and made of impact-resistant materials or reinforced with gratings.
Environmental Hardening:
Beyond physical security, shacks must be hardened against environmental factors. This includes weatherproofing, rodent-proofing, and ensuring that ventilation systems are designed to prevent unauthorized access or the ingress of contaminants.
Surveillance and Deterrence
Visible security measures can significantly deter opportunistic intruders.
CCTV Systems:
Comprehensive Closed-Circuit Television (CCTV) systems, strategically placed to cover all approaches to the shack, entrances, and surrounding areas, provide constant monitoring and evidence collection capabilities. Night vision and thermal imaging cameras can extend effectiveness into low-light conditions.
Motion Detection Systems:
These systems can trigger alarms when movement is detected within a secure zone, alerting security personnel or local authorities. This acts as an early warning system, much like tripwires in a historical fortress.
Lighting:
Adequate and well-placed lighting around the shack perimeter and access points can deter intruders by eliminating hiding spots and improving the effectiveness of visual surveillance.
Electronic and Cyber Security: Defending the Digital Frontier

While physical security protects the gateway, the true battle for secure communications often takes place in the digital realm, within the shack itself.
Network Security and Access Control
The internal network and the equipment within the shack must be protected from unauthorized digital access.
Firewalls and Intrusion Detection Systems (IDS):
Robust firewalls are essential to control network traffic, blocking unauthorized access attempts. Intrusion Detection Systems monitor network activity for malicious patterns and alert administrators to potential breaches. These systems act as the electronic gatekeepers, scrutinizing every digital visitor.
Secure Network Protocols:
Utilizing encrypted communication protocols for any internal network management or remote access is paramount. This ensures that data transmitted over the network remains confidential.
Access Control Lists (ACLs) and Authentication:
Strict access control lists should govern which devices and users can connect to the shack’s internal network. Multi-factor authentication for remote access adds an extra layer of security, requiring more than just a password for entry.
Equipment Hardening and Vulnerability Management
The individual pieces of equipment within the shack must be secured against cyber threats.
Regular Software Updates and Patching:
Manufacturers regularly release updates to fix security vulnerabilities in their equipment. Failing to apply these patches leaves the system exposed, like an unpatched hole in a ship’s hull.
Disabling Unused Services and Ports:
Any network services or ports on the equipment that are not actively used should be disabled to reduce the attack surface. Each enabled service is a potential entry point.
Strong Password Policies:
Implementing and enforcing strong, unique passwords for all access to equipment and network devices is a fundamental, yet often overlooked, security measure.
Encryption: The Cloak of Invisibility
Encryption is the cornerstone of modern secure communications, transforming readable data into an unintelligible cipher.
End-to-End Encryption:
Ideally, data should be encrypted at its origin and only decrypted at its final destination. This protects the data even if intermediate nodes, like microwave relay shacks, are compromised. This is like sending a message in a locked box that only the intended recipient has the key to.
Link Encryption:
In some cases, encryption is applied to the microwave link itself. While not as robust as end-to-end encryption, it provides a significant level of security against interception on that specific segment. This is akin to encrypting the conversation between two individuals, even if others can see them talking.
Key Management:
The secure generation, distribution, storage, and rotation of encryption keys are critical. Compromised keys render even the strongest encryption useless. This is the guardian of the lock and key, ensuring only authorized hands ever touch them.
Microwave relay intercept shacks have played a crucial role in intelligence gathering, allowing agencies to monitor communications over vast distances. For a deeper understanding of how these systems operate and their historical significance, you can explore a related article that delves into the intricacies of electronic surveillance. This resource provides valuable insights into the evolution of interception technology and its impact on modern warfare. To read more about this fascinating topic, visit this article.
Operational Security and Human Factors: The Human Element as a Shield
| Location | Number of Shacks | Distance between Shacks | Relay Capacity |
|---|---|---|---|
| City A | 10 | 5 miles | 100 Mbps |
| City B | 8 | 3 miles | 80 Mbps |
| City C | 12 | 7 miles | 120 Mbps |
Technology alone cannot guarantee security. The human element—the people who operate, maintain, and access these facilities—plays a crucial role.
Training and Awareness Programs
Investing in comprehensive security awareness training for all personnel is vital.
Security Protocols and Procedures:
Personnel must be thoroughly trained on all relevant security protocols, including access control procedures, incident reporting, and emergency response plans. They are the frontline defenders.
Threat Recognition:
Training should educate staff on recognizing potential security threats, such as suspicious individuals, unusual activity, or signs of tampering, and empower them to report these observations promptly.
Cybersecurity Best Practices:
Regular training on cybersecurity best practices, including phishing awareness, secure password management, and the importance of reporting suspected cyber incidents, is essential.
Access Control and Personnel Vetting
Controlling who has access to relay shacks and the information they carry is paramount.
Background Checks:
Thorough background checks, including criminal history and potentially more in-depth vetting for personnel with access to highly sensitive operations, are crucial. Trust is the bedrock upon which access is granted.
Role-Based Access Control:
Access privileges should be granted on a need-to-know basis, ensuring that individuals only have access to the systems and information necessary for their job functions. This minimizes the impact of a single compromised account.
Visitor Management:
Strict procedures for managing visitors, including registration, escort policies, and time-limited access, are necessary to prevent unauthorized entry.
Incident Response and Disaster Recovery
Having well-defined plans in place for responding to security incidents and recovering from disruptions is essential.
Incident Response Plans (IRPs):
Detailed IRPs outline the steps to be taken in the event of a security breach, sabotage, or major disruption. These plans should include communication protocols, containment strategies, and remediation steps.
Disaster Recovery Plans (DRPs):
DRPs focus on restoring critical communication services after a major event, whether it’s a natural disaster, a cyberattack, or a physical sabotage. This includes backup systems, redundant infrastructure, and prioritized restoration efforts.
Regular Drills and Exercises:
Conducting regular drills and exercises to test the effectiveness of IRPs and DRPs ensures that personnel are prepared to act decisively in a real crisis. These are the fire drills of the information age.
The Evolving Landscape: Future of Microwave Relay Shack Security
The threats to communication infrastructure are not static. As technology evolves, so too must the security measures employed to protect it.
Advancements in Encryption and Authentication
The pursuit of stronger and more resilient encryption methods continues.
Quantum-Resistant Cryptography:
As quantum computing capabilities advance, current encryption methods may become vulnerable. Research and development into quantum-resistant cryptography are crucial for future-proofing communications.
Biometric Authentication:
Biometric authentication methods, such as fingerprint or iris scanning, offer a more secure and convenient alternative to traditional passwords, though their implementation requires careful consideration of privacy.
Integration of AI and Machine Learning
Artificial intelligence and machine learning are increasingly being used to enhance security.
Proactive Threat Detection:
AI algorithms can analyze vast amounts of network traffic and security logs to identify subtle anomalies and predict potential threats before they materialize. This is the sentinel that never sleeps, constantly sifting through data.
Automated Incident Response:
AI can automate certain aspects of incident response, such as quarantining infected devices or blocking malicious IP addresses, allowing human operators to focus on more complex tasks.
Secure Network Architectures
The very design of communication networks is evolving to incorporate security from the outset.
Zero Trust Architecture:
This model assumes that no user or device can be trusted by default, regardless of their location or previous interactions. Every access request is verified, creating a more secure perimeter.
Software-Defined Networking (SDN):
SDN allows for more dynamic and programmable control over network traffic, enabling rapid responses to security threats and the implementation of granular security policies. This allows the network to adapt and reconfigure itself on the fly.
The security of microwave relay intercept shacks is not a singular, static solution but an ongoing process. It requires a holistic approach that integrates robust physical security, sophisticated electronic and cyber defenses, and a well-trained and vigilant human element. As the reliance on uninterrupted communication grows, so too does the imperative to ensure that these silent sentinels, and the vital information they carry, remain secure from all threats, both seen and unseen. The integrity of our digital world depends on it.
FAQs
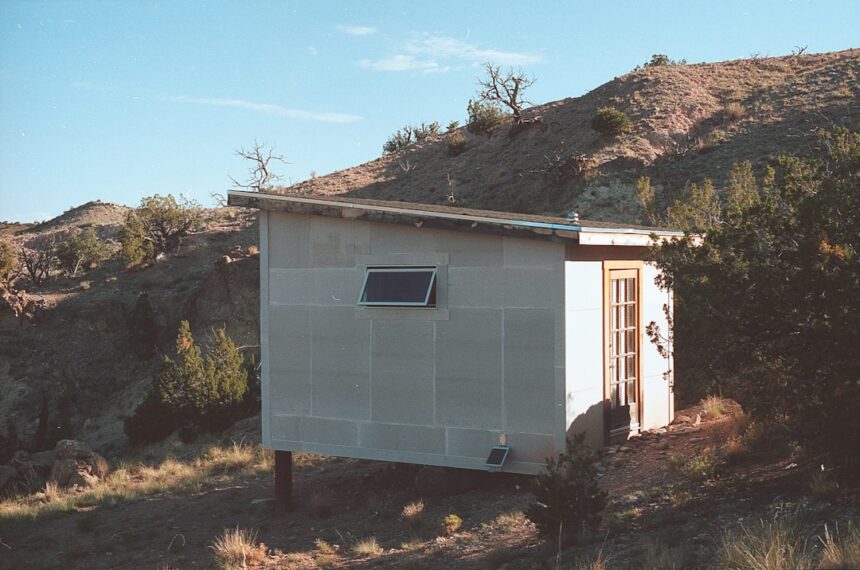
What are microwave relay intercept shacks?
Microwave relay intercept shacks are small structures used to intercept and relay microwave signals. These shacks are typically located in remote areas and are used for various purposes, including communication interception and intelligence gathering.
How do microwave relay intercept shacks work?
Microwave relay intercept shacks work by intercepting microwave signals that are being transmitted between two points. The shacks are equipped with specialized equipment that allows them to capture and analyze these signals, providing valuable information to the operators.
What are the uses of microwave relay intercept shacks?
Microwave relay intercept shacks are used for a variety of purposes, including military intelligence gathering, communication monitoring, and surveillance. They are often strategically placed in areas where they can intercept important signals and provide valuable information to the operators.
Are microwave relay intercept shacks legal?
The legality of microwave relay intercept shacks depends on the specific laws and regulations of the country in which they are located. In some cases, these shacks may be operated by government agencies for lawful intelligence gathering purposes. However, their use may also be subject to strict regulations and oversight.
What are the potential concerns associated with microwave relay intercept shacks?
Some potential concerns associated with microwave relay intercept shacks include privacy issues, as they have the capability to intercept and monitor private communications. Additionally, there may be concerns about the potential misuse of intercepted information and the impact on civil liberties.